- Technical Forums
- :
- Smart Cameras
- :
- Re: Role-based Camera Permissions for SSO/SAML
Role-based Camera Permissions for SSO/SAML
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Role-based Camera Permissions for SSO/SAML
We have another new feature for you this week! The dashboard now supports role-based camera permissions to allow organizations to use SAML/SSO for camera users. This was a much requested feature, which will allow organizations to more easily scale their MV camera deployments.
Camera Roles versus local Camera-only admins
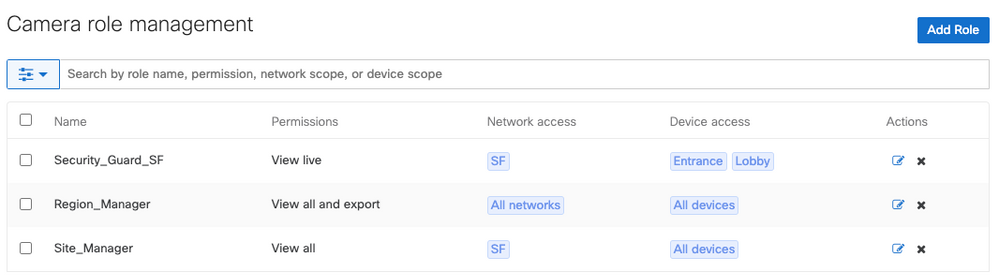
With the addition of Camera roles, there are now two types of camera accounts within the dashboard. Both types of roles provide the ability to specify viewing permissions, as well as set which cameras that a user can access.
Camera-only admins must be configured individually, per network. If you wanted to give a user access to cameras on two different networks, a role would have to be created for them on each of the target networks. This may be a manageable process for one-off role creation, or organizations with few camera users, but it doesn’t scale well. For example, if you have two users that need camera permissions on two networks, you would have to create four separate roles for them, even if their permissions were identical.
The new Camera Roles eliminates this scaling challenge and provides an easier path to adoption for large organizations with many users. You no longer need to configure accounts for each individual user in each individual network that they need access. Now, you can create roles that grant camera access within a network, or across a group of networks, and apply those roles to as many people as needed.
Configuring Camera Roles
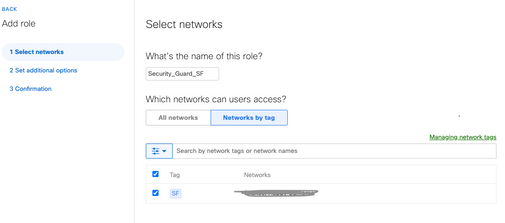
Role-based camera permissions require that you first enable SAML 2.0 and configure your SAML Identity Provider (IdP) settings within the organization. Once that is done, navigate to Organization > Configure > Camera roles and select "Add Role" to get started.
For each role, select the name, and the target networks that the role will be able to access. You can choose all networks, or networks based on tags. Next, you will have the option to set camera permissions (view and export any footage, view any footage, or view live footage only. Finally, choose the cameras that this role should be able to access. You select all cameras, or cameras based on tag.
Considerations with Camera Roles
There are a few things that need to be considered with respect to Camera Roles:
- SAML user roles map 1:1 to roles defined within the dashboard
- A SAML user can only map to a single SAML role within the dashboard
- SAML Network/Organization Admin roles are still supported, and Network/Org admins take precedence and they are matched first.
- Steps should be taken to avoid conflicts, and ensure that users only have a single SAML role passed to the dashboard to guarantee that the correct role is applied.
For more information, please see the Camera Roles documentation.
So what do you think of the new Camera Roles? We would love to hear your feedback!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Finished setting up new SAML camera roles today using G Suite as the IDP. It worked very well. Added the app to users Google waffle by groups for one-click sign in to the Meraki Dashboard.
Once caveat though, the Meraki dashboard will only accept a sha1 fingerprint and G Suite only offers up a sha256 fingerprint in a SAML app. The certificate itself can be either, but not the fingerprint. I used a sha calculator off of the one login site to assist in converting the G Suite certificate to a sha1 fingerprint. At that point, the Meraki dashboard accepted my fingerprint and things flowed smoothly.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @BrothersTM that's great! I'll pass along the feedback about the fingerprint compatibility between the dashboard and G Suite, but glad you were able to figure out a workaround for now.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi, for me ot only works for organisation or network administrators. But how can I map them to SAML roles?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I followed the procedures from this article:
Also, our school district uses G Suite so I then created a SAML app within the Google Admin Console for one click SSO for my Meraki Camera admins. The article below details that process.
https://support.google.com/a/answer/7623669?hl=en
I use AD groups that map to Google groups via their sync tool. In the assigning of the SAML app, I then assign it to the groups so that I only have to add/remove users from the AD group in order for them to have access to certain cameras.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have followed the same document. I followed all the steps until I come to the configuring local Camera-only admins.
I can't add the SAML role that I have created as admin neither can't I add an admin who is part of the SAML role. I can add this role to a Administrator located within the Meraki dashboard but not from SAML.
Maybe I get something very wrong 🙂
And, what do I need to choose when creating a SAML role? I use Azure as IDP
Thank you for your help.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Saralyn I have also opened a case regarding Camera roles but feel like I should write here ...
It would be great that Meraki try to follow a standard concept over all functionalities in the dashboard. One such concept would be - what characters can contain a role name.
Standard SAML roles can have spaces - so I have designed all my roles (40+ roles across 10+ orgs) with spaces and had some magic filtering in ADFS. Now when Camera roles were introduced - they don't allow spaces, which makes them useless for me, unless I redesign the naming concept and remove spaces from all role names.
So, please look into this and try to follow a standard in the dashboard...