Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Security appliance has detected a rogue DHCP server
Security appliance has detected a rogue DHCP server
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Security appliance has detected a rogue DHCP server
Hi there,
Once a week we get an alert:
The security appliance in the Redacted - appliance network has detected a rogue DHCP server in your network.
A rogue DHCP server was found on VLAN 1 serving addresses with the subnet redacted/24. The server has MAC address redacted and IP redacted
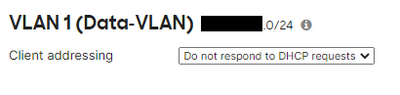
The MAC and IP it shows are for a Windows server on the network that is the legitimate DHCP server for the network. The security device itself is set to ignore DHCP requests on VLAN 1. I have checked the DHCP servers & ARP page under switch and the DHCP server is listed there as allowed.
I would like to be able to stop these false positives without turning the rogue DHCP detection off completely. Does anyone know of a way to do this?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Are you sure DHCP (including relay) on the MX is completely disabled on that VLAN?
It doesn't usually falsely alert.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Does the specified IP really match the IP address? I'd assume that something like teaming is in place that changes the MAC <-> IP binding.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @CptnCrnch
The DHCP server in question is a VM. Neither the VM or it's host server use NIC teaming. I've confirmed the IP and the MAC address in the alert corresponds to the same on the VM.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sorry for the dumb question, but is this server listed as "Allowed"?
https://documentation.meraki.com/MS/Monitoring_and_Reporting/MS_DHCP_Servers#Allowed_DHCP_Servers
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@CptnCrnch there are no dumb questions 🙂
I did check this and the server is there with the correct IP, MAC address and hostname.I would post a screenshot but I'd have to redact half of it.
-
3rd Party VPN
163 -
ACLs
88 -
Auto VPN
287 -
AWS
35 -
Azure
66 -
Client VPN
368 -
Firewall
833 -
iOS
1 -
Other
540 -
Wireless LAN MR
1