- Technical Forums
- :
- Security & SD-WAN
- :
- Re: S2S VPN to non-Meraki router broken after MX100 upgraded to v15.43
S2S VPN to non-Meraki router broken after MX100 upgraded to v15.43
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
S2S VPN to non-Meraki router broken after MX100 upgraded to v15.43
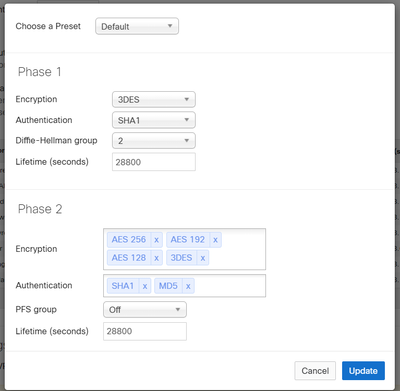
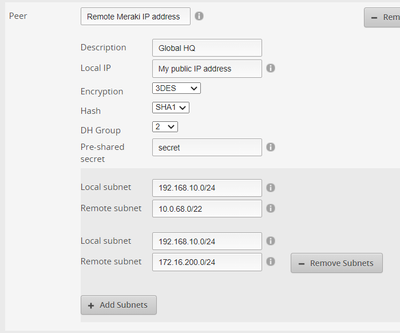
Our MX100 firmware was upgraded to v15.43 this morning (auto upgrade, not manual). Ever since one of our remote workers with a Ubiquiti EdgeMAX router at home can no longer get the site-to-site VPN tunnel to work. It does not employ DES so that is not the issue. Here are the settings on the Meraki for the connection:
And the Ubiquiti:
This VPN tunnel worked fine prior to the upgrade. So what did the upgrade break and how do I fix it? This remote worker also cannot get the Client VPN to work. If he uses his Verizon hotspot the Client VPN works. If he tries the Client VPN on his home wifi or wired network connections it fails.
I did open a support ticket but thought I might get a quicker response from the Community due to the issues Meraki is experiencing today.
Thank you.
- Labels:
-
3rd Party VPN
-
Client VPN
-
Other
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
https://documentation.meraki.com/MX/Site-to-site_VPN/Site-to-Site_VPN_Settings#Non-Meraki_VPN_peers
If you found this post helpful, please give it Kudos. If my answer solves your problem please click Accept as Solution so others can benefit from it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Since that field was empty before, what should I enter there, the remote public IP address, the private IP address of the remote Ubiquiti, or ??
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
it'll depend on what the other end is/supports. i'd start with trying the public IP of the far end device. or, if that device is behind a nat it might want the private/real IP. it should be whatever the ubquiti considers its local ID.
If you found this post helpful, please give it Kudos. If my answer solves your problem please click Accept as Solution so others can benefit from it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It's not behind a NAT, it is the router connected to his cable modem. It literally IS the device creating the NAT. As I said, it is a Ubiquiti EdgeMAX router.
So how would one go about trying to find this mysterious "Remote ID"? We have never used anything in the Local ID or Remote ID fields for site-to-site VPN connections to non-Meraki devices.
Here is what I am seeing in the Event Log:
msg: IPsec-SA expired: ESP/Tunnel GLOBAL_HQ_PUBLIC_IP[4500]->REMOTE_UBIQUITI_PUBLIC_IP[4500] spi=3329526648(0xc6748b78)
msg: IPsec-SA expired: ESP/Tunnel REMOTE_UBIQUITI_PUBLIC_IP[4500]->GLOBAL_HQ_PUBLIC_IP[4500] spi=52183207(0x31c40a7)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
i'd start by entering the public IP of Ubiquiti
If you found this post helpful, please give it Kudos. If my answer solves your problem please click Accept as Solution so others can benefit from it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Did not work. Private IP of router did not work. Nothing I have tried works.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm going to go out on a limb and say your issue is probably due to the much greater Meraki Cloud Certificate issue that everyone else is going through today. The issue specifically effects VPN tunnels. I went on to the community to see if there were any updates and came across your post so I figured I weight in.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
sounds like a support case will be needed here so they can take a deeper look at it
If you found this post helpful, please give it Kudos. If my answer solves your problem please click Accept as Solution so others can benefit from it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
also, you can rollback to 15.42.1 if the s2s vpn was stable on that release. i would still of course recommend a support case to look into the issue on 15.43.
If you found this post helpful, please give it Kudos. If my answer solves your problem please click Accept as Solution so others can benefit from it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I don't know how to rollback the firmware. I've had a case open for 6 hours; no response yet.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
it's very straightforward
If you found this post helpful, please give it Kudos. If my answer solves your problem please click Accept as Solution so others can benefit from it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Downgrading the firmware fixed the problem. I'll leave it as is and work with support once they respond to the request.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
even meraki peers got bricked by this update.
got a mx100 as host with mx60s as spokes. services on the other mx60s can't access servers hosted on mx100.
rolled back to previous. fixed it like nothing happened.
-
3rd Party VPN
169 -
ACLs
102 -
Auto VPN
322 -
AWS
39 -
Azure
73 -
Client VPN
449 -
Firewall
651 -
Other
603