Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Restricting Cellular data during failover to business critical applications...
Restricting Cellular data during failover to business critical applications on the MX64
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Restricting Cellular data during failover to business critical applications on the MX64
I found the following statement:
Cellular Failover Rules
These firewall rules are appended to the existing outbound rules when the appliance has failed over to using a cellular modem as its uplink. This can be useful for limiting cellular traffic to only business-critical uses in order to prevent unnecessary cellular overages.
In this link: https://documentation.meraki.com/MX/Firewall_and_Traffic_Shaping/Firewall_Settings
However, today our managed service provider was told by Meraki support that it was not possible when he was trying to configure. Can someone confirm which is correct? The documentation or the Meraki support rep?
Thanks for any help!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What specifically was your provider asking that had support contradict their own documentation? Need more context to be able to respond appropriately. ^_^
That being said, those Cellular Failover Rules do indeed append up if WAN 1 goes down, however they by default will only apply to an actual cellular USB device being used.
If your using say a 4G connection (mifi) that is connected into WAN2 (via Ethernet connection), the MX has no clue that the median at which it traverses is cellular. All it knows is WAN2 is WAN2.
Meraki doesn't have a specific set for WAN2 for some unknown reason (I pray one day they will add it), but in the meantime, few of us know of a trick where you can have support make the cellular rules 'act' as the WAN2 rules. However only support can enable that for you.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I agree with what @NolanHerring said. One thing I will add is that documentation is written and reviewed before being published, as apposed to a support technician that is stating something in the moment that can either have misunderstood a question, been new to the role, or even just had an "off day" and was having a hard time focusing. Don't get me wrong, Meraki support is fantastic and on the ball, but everyone is prone to human error.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The cellular failover firewall rules only apply to USB based cellular modems (or the built in cellular modems). They don't apply to cellular modems that connect via Ethernet.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks a lot for making this clear to me.
But I would have another very interesting (and at the moment theoretical) question: The documentation says "These firewall rules are appended to the existing outbound rules".
My current ruleset has the following structure:
{"protocol" | udp | "srcPort" | Any | "srcCidr" | Any | "destPort" | 53 | "destCidr" | Any | "policy" | allow | "syslogEnabled" | false | "comment" | DNS for FQDN support} |
| {"protocol" | tcp | "srcPort" | Any | "srcCidr" | Any | "destPort" | 80,443 | "destCidr" | *.microsoft.com | "policy" | allow | "syslogEnabled" | false | "comment" | HTTP[S] to MS} |
| {"protocol" | any | "srcPort" | Any | "srcCidr" | Any | "destPort" | Any | "destCidr" | Any | "policy" | deny | "syslogEnabled" | false | "comment" | Default catch-all other traffic} |
| {"protocol" | Any | "srcPort" | Any | "srcCidr" | Any | "destPort" | Any | "destCidr" | Any | "policy" | allow | "syslogEnabled" | false | "comment" | Default rule} |
(rule #2 has been capped for demo purposes)
That said my question would be: Where are the Cellular Failover Rules "appended"?
- Before or after rule #4 (which is the default rule that cannot be changed)?
- Before or after rule #3 (which I had to insert in order to block unwanted outgoing traffic: I'm not very happy with the default rule #4 -- this is NOT the best practice for firewalls)?
How can I control this? How can the Cellular Failover Rules do what they're supposed to do (e.g. deny traffic to microsoft.com, because you don't want to update your device using an expensive cellular service billed by volume)?
Rgds, Andreas
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
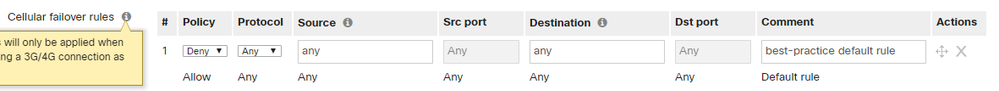
Look here (this screenshot is not taken from the docu, but from the very original page where you configure the rules):
To me, this now very much looks like the "Cellular failover rules" shall simply substitute the native outbound rules!
This would make sense in some respect -- and of course render my last Message obsolete...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
...and by the way: this rule section would not accept a "FQDN support" type of firewall rule -- neither by GUI nor by API!
Therefore, I requested this feature to be added via "Make a Wish" today: When disaster strikes (i.e. primary internet access WAN1 is gone) you need to be able to control which kind of business critical traffic (most of these are cloud based Web services) you still want to Allow or Deny.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Let's assume for a moment that "Cellular failover rules" simply substitute the native "Outbound rules" (which would a bad idea since they do not support FQDN, but this is another story).
Given that, every admin should at least add the following rule as new rule #1 (i.e. BEFORE the default allow-any-any-rule is matched):
Otherwise, your SIM card will get a very high bill!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello, did you find a solution for this?
-
3rd Party VPN
170 -
ACLs
91 -
Auto VPN
296 -
AWS
36 -
Azure
68 -
Client VPN
379 -
Firewall
849 -
iOS
1 -
Other
547 -
Wireless LAN MR
1