- Technical Forums
- :
- Security & SD-WAN
- :
- Re: PCI VA Scan results and port traffic
PCI VA Scan results and port traffic
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
PCI VA Scan results and port traffic
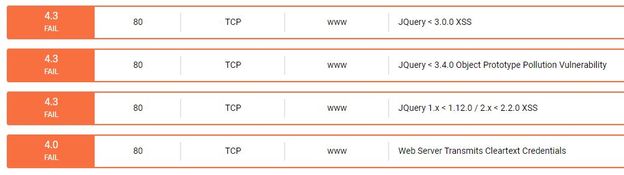
We recently had all 28 of our network scanned for vulnerabilities as part of our annual PCI audit. We have the same model MX and the same firewall rules in place on all 28 networks. The findings were interesting. Almost exactly half of the networks failed the scan due to vulnerabilities for TCP traffic on port 80.
If my firewall rules are all the same, and the devices on the network are 95% the same, why would half of the networks fail the scans and the other half pass?
Why doesn't IDS or IPS see the port scanning and block it?
I'm sure there are a million variables that could cause the pass/fail variances between theoretically identical network configs, despite that any ideas would be helpful.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Your scan is probably being triggered by the Local Status Page on the MX.
You can disable it under Network-wide > General if you're not using them.
There was a security vuln with these pages last year as well. Are all your MX on the same version?
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20181107-meraki
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Are there webserver or webservices behind those networks that failed? Vulnerability could be found with those applications/services and not the MX, if it allowing the traffic needed.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This was a scan from the outside right? And the MX's have a NAT from the outside to a server on the inside?
As @SoCalRacer says, this is probably an issue on those servers.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@PhilipDAth yes scan from the outside, no NAT to server on the inside, in fact no servers on this network.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
no web servers or failing web services
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
-
3rd Party VPN
168 -
ACLs
101 -
Auto VPN
314 -
AWS
39 -
Azure
70 -
Client VPN
430 -
Firewall
711 -
Other
592