Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Outbound Firewall not blocking internal users, only works on users connecte...
Outbound Firewall not blocking internal users, only works on users connected via VPN?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Outbound Firewall not blocking internal users, only works on users connected via VPN?
Trying to determine if the built-in Layer 3 firewall at Security & SD-Wan > Firewall would be preferable to Umbrella's firewall offering, I set up some rules to do some testing. I created a bunch of TCP allow ports for standard stuff like http and https and a blanket deny at the bottom of the Output rules section (Inbound just has one Default deny/deny any/any rule). Once I saved the configuration I did some testing on several machines on our LAN only to discover that nothing was being blocked as expected. However, a few minutes later, I started getting complaints from users connected via Secure Client/Any Connect that they couldn't reach any of our internal http/s services or SMB shares. Turns out I forgot to add 53 for DNS. Once added, their connections started working again.
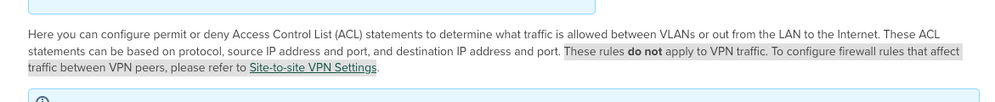
However, this told me that for some reason, the firewall rules were only applying to connections coming through the VPN. This is especially strange because the documentation says that the layer 3 firewall rules will NOT affect VPN:
We are using Hub and Spoke with only 1 spoke but I've been only testing with AnyConnect so far.
A) Does anyone know why it would be better to use Umbrella for our firewall stuff? We don't have any DMZ or public-facing services, just want the extra security of being able to block all outbound traffic and selectively let through only what is necessary. The challenge with Umbrella is it needs to be set up via tunnel which I'm afraid would impact our users negatively (we need all traffic including Spoke SD-Wan, AnyConnect, and LAN to always come from the same WAN IP) if it was tunneling traffic away from or obscuring out WAN IP address (need to maintain cookies for users or else they would face MFA prompts all day when trying to do their work).
B) Am I missing or miss-configuring or missunderstanding how the built-in Meraki layer 3 outbound firewall should be working? Why would the firewall be blocking outbound connections coming from the AnyConnect Secure Client but not connections coming from the LAN itself?
- Labels:
-
Firewall
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is your Default route set to pass traffic to Umbrella via a tunnel?
(worth clarifying what mean by Umbrella too - are we talking SIG or Secure Connect?)
Bear in mind too that, depending on the MX firmware and what traffic is involved, deny might take a little while to kick in.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the reply.
No, the tunnel is currently off because of the concerns mentioned re: losing WAN IP consistency hence I'm testing the built-in Meraki firewall stuff to see if it would work in place.
We have the full Umbrella suite so we do have Umbrella SIG Advantage and are using DLP and IPS protection, but the Umbrella firewall stuff is not active beyond that (0 hits in the last 30 days).
Not sure what you mean by SIG or Secure Connect...as mentioned, the Meraki firewall rules are applying to users that are VPN'ing in via AnyConnect Secure Connect Client, but are not affecting users on the LAN or SD-Wan.
I have had the rules set for a few hours now and still am experiencing the same thing--LAN/SD-Wan are not being affected by any of the firewall rules (e.g. I have a http service out on the web on a non-standard port that I can reach fine from the LAN/SD-Wan, but if I VPN into the HUB with Cisco Secure Client, while connected, I cannot reach said service).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Umbrella SIG is Secure Internet Gateway, more info here: Learn about our Secure Internet Gateway (SIG) - Cisco Umbrella
I'm thinking you are using the traditional integration with the MX?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We are Paying for Umbrella SIG Advantage. https://documentation.meraki.com/MX/Site-to-site_VPN/MX_and_Umbrella_SIG_IPSec_Tunnel but it is not configured as mentioned because we need to keep static IP addresses. We were going to test this functionality, but never did get that far (AT&T will just stop replying to tickets and it's been 9 months of torture trying to get them to help get this all working). From what I read in that article, it seems like it indeed will change our Public IP which is something we can't do. (Technically it is partially configured, they created the tunnel but it is not established or up and running).
That said, I do have Intelligent Proxy and SSL decryption enabled on all of our policies and all Secure Clients have Umbrella installed and enabled. As far as I understand, though, the firewall policies in Umbrella won't have any affect without the Tunnel up and running hence the all are registering 0 hits over the last 30 days).
I was kind of hoping that in the interim I could use the built-in Meraki firewall rules to at least get some cover for an upcoming audit, but it only seems to be applying to the SD-Wan users and users connecting via Secure Client, the rest of the users on the LAN aren't affected by these settings as far as I can tell (tested by trying to get to an external http service I have running on an unconventional port out on DigitalOcean; I can reach it fine on the LAN despite there being no "allow" rule for this port but when connected via Secure Client and or on the SD-Wan network, I cannot access the site indeed).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It's really difficult to be able to help here without visibility of your Dashboard. Basically I'd call Meraki Support on the phone and work through a case with them - firewall rules should apply to all users connected via a VLAN having that MX as their Default Gateway - assuming said traffic is routed, rather than bridged.
Contact details via ? > Get help & cases in the Dashboard - then click the MX tile and follow either Call support team or Call me now, bottom right
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Unfortunately, we are leasing everything through AT&T so that is where I'm supposed to get support (they haven't been very helpful to put it mildly). I have had other Meraki Employees here seem to be able to get in and view our setup before, can you not?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
IF you have multiple VLANs at your site - or tunnels that go somewhere other than SIG - the MX can provide protection related to those flows that never hit SIG. You need tunnels to SIG (or some other central breakout) because of the apparent need to use a common source IP. I would certainly be pushing your SaaS providers as to why they still insist on this though, TBH. But - by funnelling everything through SIG, you also get a more common approach to security, all managed in one place and applied 'near you' (your Cisco DC, wherever you are). Cloud security such as SIG also offers greater scalability than a small appliance - particularly useful for intensive processes, such as TLS decryption.
You might also want to progress on from SIG to Cisco Secure Connect, which is effectively SIG in the Meraki Dashboard, but with added capability for centralised secure remote access also using that common policy - no need to choose any particular MX to point AnyConnect client at...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the excellent and thorough reply.
Unfortunately, we purchased Meraki/Umbrella through AT&T so I don't have full admin access to stuff. Additionally, they have be absolutely abysmal with help getting things set up. It's been almost a year, and still things are not functioning correctly and it's quite expensive. I just wish expensive enough to get a lawyer to see if we could get out of the contract. This is why I'm trying to learn/do this stuff myself (the whole point was to offload this kind of work so that I could focus on other things and be assured that things are configured correctly).
@GreenMan wrote:I would certainly be pushing your SaaS providers as to why they still insist on this though, TBH.
This isn't due to SaaS providers, we work in Financial Services which requires us to log in to many financial accounts on behalf of our clients. We get initial permissions and things set up and then try our hardest to keep things running without having to keep bothering our clients. If we are constantly losing our MFA tokens etc. we would be having to bother them constantly or at least every time we tried to log in and the user appeared to be coming from a new/different WAN IP address. We are a service business so keeping our clients happy is key hence we try to consolidate all of our traffic (and have been for years) partly for this reason. The other as you mentioned is it makes it easier to consolidate monitoring and security management.
I wish I understood enough what the differences are in what we are using vs what you mentioned. I do have Intelligent Proxy and SSL decryption enabled on our policies and we are using Cisco Secure Connect and Umbrella is active and enabled on all of the clients. I don't understand, though, how this fits in with the firewall configuration. It looks like you may be referring to where a tunnel is set up and traffic is tunneled offsite to SIG as explained here: https://documentation.meraki.com/MX/Site-to-site_VPN/MX_and_Umbrella_SIG_IPSec_Tunnel This seems to confirm that it does indeed change the WAN IP address so not sure how/if this could work for us.
Again, still curious as to if the built-in firewall could at least offer us some protection in the interim, but for whatever reason it still appears to be only affecting users who are connecting via VPN and/or the SD-Wan users.
-
3rd Party VPN
170 -
ACLs
91 -
Auto VPN
296 -
AWS
36 -
Azure
68 -
Client VPN
380 -
Firewall
850 -
iOS
1 -
Other
549 -
Wireless LAN MR
1