- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Meraki Site-to-Site VPN Setup for Multiple Networks
Meraki Site-to-Site VPN Setup for Multiple Networks
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Meraki Site-to-Site VPN Setup for Multiple Networks
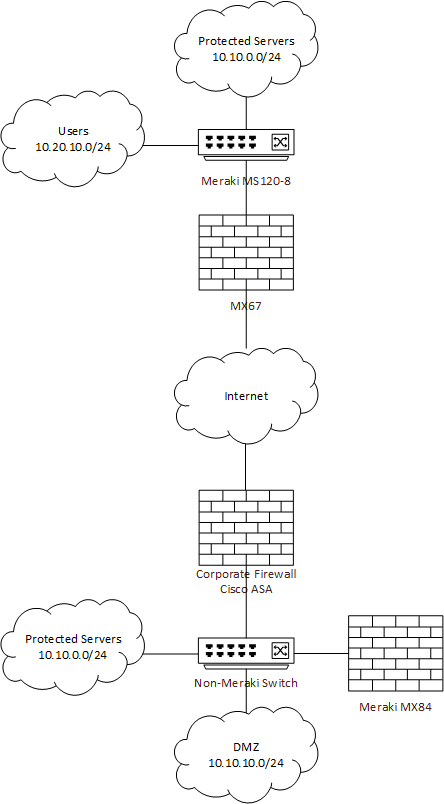
I am managing the above network, which consists of a corporate office and one branch. The branch is connected to the internet via an MX67 in routed mode, configured as a S2S VPN Spoke with automatic NAT traversal. It currently only has users, so it is in Single LAN mode.
The corporate network is behind a Cisco ASA. All the networks in the corporate office are L2 up to the ASA. The MX84 currently has a P2P link to the ASA over its own VLAN. This MX84 is in passthrough / VPN concentrator mode, with the S2S VPN set as a hub and NAT traversal as automatic.
At this time, users in the branch office can reach the DMZ in the corporate office over the S2S VPN, via the MX67 and then the ASA, as they should. The goal is to add the protected servers network to the branch office, and let it reach the already-existing protected servers VLAN in the corporate office. This network is on its own VLAN (1000) and no other networks should be able to reach it unless permitted by the ASA.
Users in the branch should continue to be able to reach the DMZ at corporate, as well as the internet via split-tunnel configuration already present in the S2S configuration.
I think I'll need to continue with the MX67 as gateway for the branch. I assume I'll need to change it to have multiple VLANs, one for users and one to match the protected servers VLAN at corporate. Then, can I just trunk those VLANs from the ASA to the MX84? What should my configuration look like for the MX's? Finally, when I'm making these changes, is it possible to break the Meraki configurations from the dashboard enough to lose connectivity to the firewalls (and if this happens, how can I revert)?
The networks shown are not accurate to the network in reality, and there are multiple networks on each side that will need this configuration. Thank you.
- Labels:
-
Auto VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Are you placing servers at the branch or you mean you just need branch users to access the servers VLAN at corp? If the latter you would just need to advertise the servers subnet via the hub so it will be in the spoke route table and know to use the VPN path.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
There are protected servers at both corp and the branch. They should be totally separate from the users. If I need a user to ever reach a protected server, I'd like to configure that in the ASA. The protected servers at the branch should be able to talk directly to those at corp. The users in both corp and the branch should be able to route via the ASA to reach DMZ servers (which also shouldn't be able to reach protected servers).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Bumping this topic.
-
3rd Party VPN
171 -
ACLs
101 -
Auto VPN
318 -
AWS
39 -
Azure
72 -
Client VPN
434 -
Firewall
727 -
Other
599
