Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Re: MX64 - Allow only Office 365 when using WAN-2(Fail-over).
MX64 - Allow only Office 365 when using WAN-2(Fail-over).
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MX64 - Allow only Office 365 when using WAN-2(Fail-over).
I am working on firewall rules to allow only office 365 when using WAN-2. My Failover is WAN-2 and my network has 3 different VLAN's Main, Client, Crew. All traffic is allowed when using my WAN-1 and when WAN-1 goes down Failover need to be active.
WAN-1 allow all the traffic.
WAN-2(Failover) allow Mian and block Client, Crew. Main should have only access to Office 365 to send emails and block everything else.
WAN-1, WAN-2 use different Public IP.
Any help will be appreciated to achieve the above task.
Regards.
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
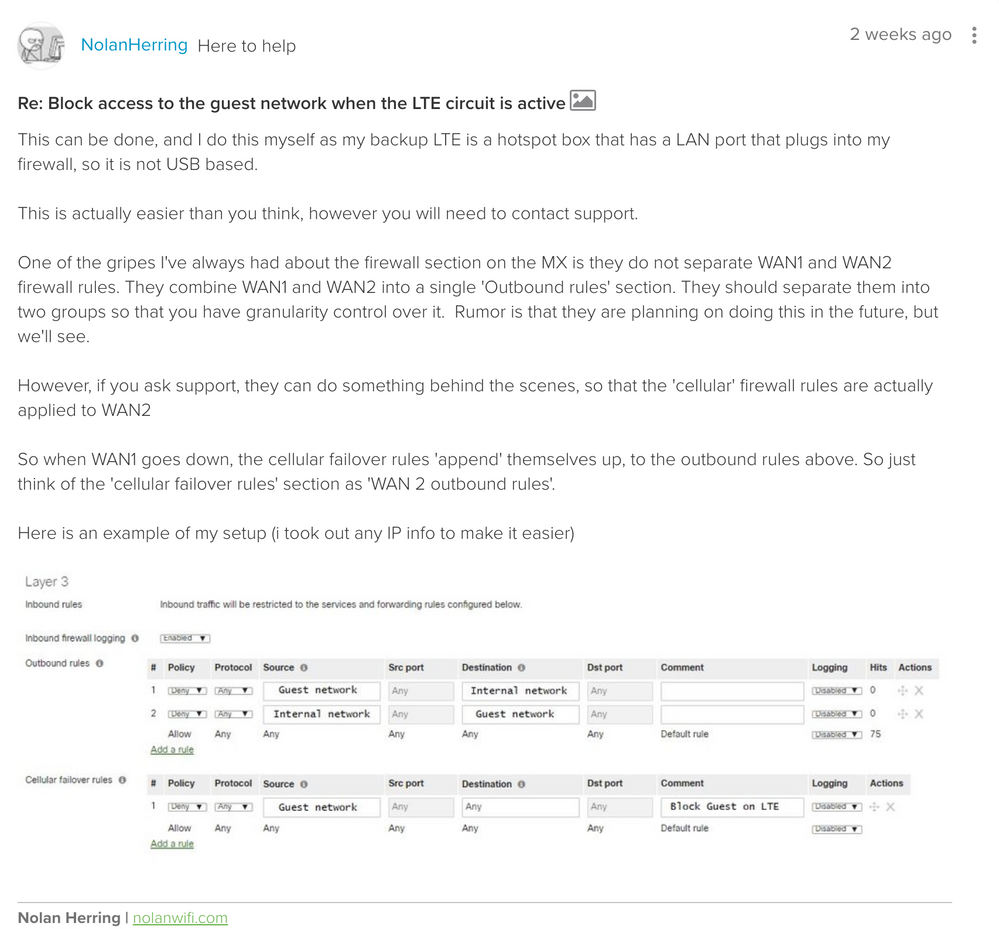
In another thread from about 2 weeks ago @NolanHerring mentioned you can have support change WAN 2 to act as the failover which allows you to set the "Cellular failover" firewall rules to apply when the MX fails over to WAN 2. That would allow you to deny everything, but Office 365 when on your WAN 2.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In another thread from about 2 weeks ago @NolanHerring mentioned you can have support change WAN 2 to act as the failover which allows you to set the "Cellular failover" firewall rules to apply when the MX fails over to WAN 2. That would allow you to deny everything, but Office 365 when on your WAN 2.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@MacuserJim Thanks for the info.
I guess I need to call support and ask them to make my cellular failover rules should point to my WAN-2 when failover is active.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@MacuserJim I have called the support and everything works well except I cannot see FQDN option when I am writing cellular failover rules!! I need to allow only office 365 for my WAN-2 so I need to mention the domain name to make it work.
How can I fix this?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am not sure about that one... The best answer I have (at least right now) is to track down which IPs your office is using for Office 365 and add those and then submit a make a wish to be able to add the FQDN.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@MacuserJim WAN-2 is a metered service that is the reason I want to allow only office 365, I already submitted a wish to add FQDN.
Thank you so much for your time.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Of course. Glad I could help!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ironically, I always see OFFICE365 as one of our biggest hitters for bandwidth consumption. Its a constant complaint on Microsoft forums about how much bandwidth the constant syncing it does between client to server over the Internet. People hotspot bills getting slammed etc. I've found no solution for this.
With that being said, if you WANTED to try something. The only thing I could think of is to create an API script, that would create a new L3 firewall rule, that would allow the IP Addresses that OFFICE365 uses, and then deny any any at the end. That would do the job in theory.
their insane IP list is here
https://docs.microsoft.com/en-us/office365/enterprise/urls-and-ip-address-ranges
This would be a manual process though. You'd basically have to act on this yourself once you get an email alert from the dashboard that your primary link went down. So you would just update the L3 firewall rules via API. When WAN1 comes back, run another API script to set everything back to normal.
I don't know how you could automate this anymore unfortunately.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I spoke with the support they can't do anything to include FQDN option for cellular failover rules. As you mentioned it is one of the ways to achieve what I am looking for but I don't want to make it complicated.
Do you suggest any other solution to achieve what I am looking for except the cellular failover as WAN-2?
Regards.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
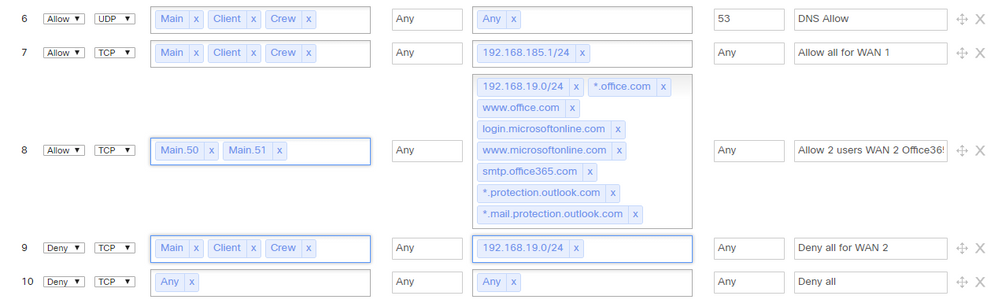
Need a suggestion from you guys.
WAN-1 allow any traffic.
WAN-2 allow only Main VLAN .50&.51 to access office 365 and block everything else.
(consider 192.168.185.1/24 as my WAN-1, 192.168.19.0/24 as my WAN-2)
I am trying to do all this on "outbound rules" will these rules help me to achieve the above scenario? If not please suggest me what needs to be added.
Regards.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What is in the subnets 192.168.185.1/24 and 192.168.19.0/24?
Are you using static IPs for your WANs?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Don't worry about the IPs I just put there as an example I will make sure I put the right IPs when testing. I want to know if my rules gonna work or not?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Review the FQDN Support here:
https://documentation.meraki.com/MX/Firewall_and_Traffic_Shaping/Firewall_Settings
Important notes:
Make sure your MX is running 13.4 or higher firmware as anything running 13.3 or earlier does not support FQDNs in the destination fields according to the documentation. You will also have to enable 'hostname visibility' for FQDN rules to function correctly, this is under the networks General settings.
I only see 13.33 as Stable and 13.36 as Stable Release Candidate currently.
My interpretation of this is that you will have to run 14.X code for putting an FQDN into the destination field for this to work (unless I'm misreading something?) 14.X code is technically beta as of 11/1/2018 so you might want to keep a closer eye on its performance etc., if you decide to move forward with this. I believe there a quiet a few people who are running 14.X for improved AMP performance/reliability without much issue.
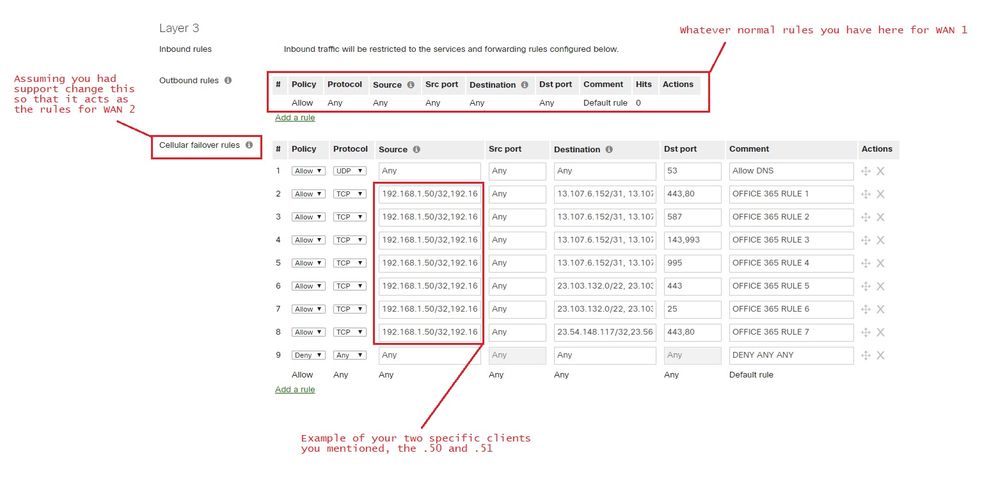
However, with all that being said. Big giant undocumented and known+expected behavior is FQDN is not supported in Cellular Failover rules, only IP addresses.
This means you will only be able to utilize IP Addresses for now to accomplish what your trying to do.
Below is my best attempt at taking the IP information from Microsoft to accomplish what the FQDN would have done on the cellular firewall rules.
You should be able to copy/paste these so it would be minimal effort to test.
OFFICE 365 RULE 1
13.107.6.152/31, 13.107.9.152/31, 13.107.18.10/31, 13.107.19.10/31, 13.107.128.0/22, 23.103.160.0/20, 23.103.224.0/19, 40.96.0.0/13, 40.104.0.0/15, 52.96.0.0/14, 111.221.112.0/21, 131.253.33.215/32, 132.245.0.0/16, 134.170.68.0/23, 150.171.32.0/22, 157.56.232.0/21, 157.56.240.0/20, 191.232.96.0/19, 191.234.140.0/22, 204.79.197.215/32, 206.191.224.0/19
OFFICE 365 RULE 2
13.107.6.152/31, 13.107.9.152/31, 13.107.18.10/31, 13.107.19.10/31, 13.107.128.0/22, 23.103.160.0/20, 23.103.224.0/19, 40.96.0.0/13, 40.104.0.0/15, 52.96.0.0/14, 111.221.112.0/21, 131.253.33.215/32, 132.245.0.0/16, 134.170.68.0/23, 150.171.32.0/22, 157.56.232.0/21, 157.56.240.0/20, 191.232.96.0/19, 191.234.140.0/22, 204.79.197.215/32, 206.191.224.0/19
OFFICE 365 RULE 3
13.107.6.152/31, 13.107.9.152/31, 13.107.18.10/31, 13.107.19.10/31, 13.107.128.0/22, 23.103.160.0/20, 23.103.224.0/19, 40.96.0.0/13, 40.104.0.0/15, 52.96.0.0/14, 111.221.112.0/21, 131.253.33.215/32, 132.245.0.0/16, 134.170.68.0/23, 150.171.32.0/22, 157.56.232.0/21, 157.56.240.0/20, 191.232.96.0/19, 191.234.140.0/22, 204.79.197.215/32, 206.191.224.0/19
OFFICE 365 RULE 4
13.107.6.152/31, 13.107.9.152/31, 13.107.18.10/31, 13.107.19.10/31, 13.107.128.0/22, 23.103.160.0/20, 23.103.224.0/19, 40.96.0.0/13, 40.104.0.0/15, 52.96.0.0/14, 111.221.112.0/21, 131.253.33.215/32, 132.245.0.0/16, 134.170.68.0/23, 150.171.32.0/22, 157.56.232.0/21, 157.56.240.0/20, 191.232.96.0/19, 191.234.140.0/22, 204.79.197.215/32, 206.191.224.0/19
OFFICE 365 RULE 5
23.103.132.0/22, 23.103.136.0/21, 23.103.144.0/20, 23.103.198.0/23, 23.103.200.0/22, 40.92.0.0/14, 40.107.0.0/17, 52.100.0.0/14, 52.238.78.88/32, 65.55.88.0/24, 65.55.169.0/24, 94.245.120.64/26, 104.47.0.0/17, 157.55.234.0/24, 157.56.110.0/23, 157.56.112.0/24, 207.46.100.0/24, 207.46.163.0/24, 213.199.154.0/24, 213.199.180.128/26, 216.32.180.0/23
OFFICE 365 RULE 6
23.103.132.0/22, 23.103.136.0/21, 23.103.144.0/20, 23.103.198.0/23, 23.103.200.0/22, 40.92.0.0/14, 40.107.0.0/17, 52.100.0.0/14, 65.55.88.0/24, 65.55.169.0/24, 94.245.120.64/26, 104.47.0.0/17, 157.55.234.0/24, 157.56.110.0/23, 157.56.112.0/24, 207.46.100.0/24, 207.46.163.0/24, 213.199.154.0/24, 213.199.180.128/26, 216.32.180.0/23
OFFICE 365 RULE 7
23.54.148.117/32,23.56.200.254/32
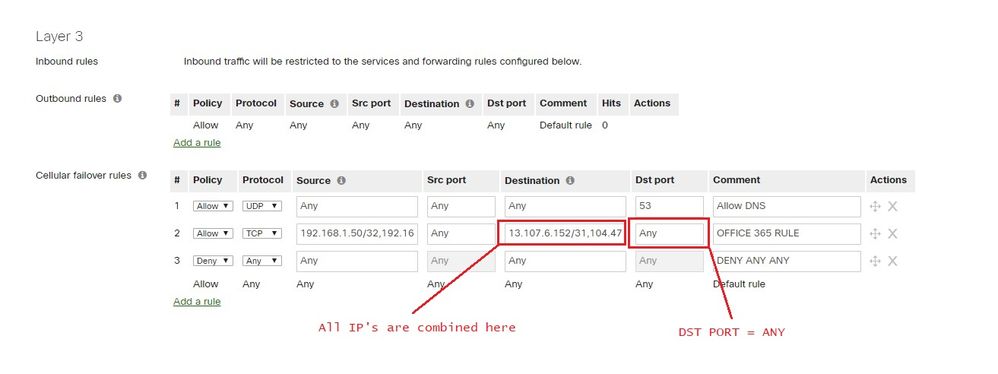
The rules above are the super specific ones that I could come up with based on the Microsoft document from the link earlier mentioned. However a good deal of these are duplicate IP's etc. So if you wanted to stream-line it, and ignore the destination port specificity, then you could do this with destination port of ANY and call it a day
OFFICE 365 RULE - ANY DST PORT
13.107.6.152/31,104.47.0.0/17,111.221.112.0/21,13.107.128.0/22,13.107.18.10/31,13.107.19.10/31,13.107.9.152/31,131.253.33.215/32,132.245.0.0/16,134.170.68.0/23,150.171.32.0/22,157.55.234.0/24,157.56.110.0/23,157.56.112.0/24,157.56.232.0/21,157.56.240.0/20,191.232.96.0/19,191.234.140.0/22,204.79.197.215/32,206.191.224.0/19,207.46.100.0/24,207.46.163.0/24,213.199.154.0/24,213.199.180.128/26,216.32.180.0/23,23.103.136.0/21,23.103.144.0/20,23.103.160.0/20,23.103.198.0/23,23.103.200.0/22,23.103.224.0/19,40.104.0.0/15,40.107.0.0/17,40.92.0.0/14,40.96.0.0/13,52.100.0.0/14,52.238.78.88/32,52.96.0.0/14,65.55.169.0/24,65.55.88.0/24,94.245.120.64/26,23.103.132.0/22,23.54.148.117/32,23.56.200.254/32
I have no clue if this would work or not work. Only one way to find out is to test it 😃
Good luck !
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I just now tested in my Lab the IPs you mentioned works well to allow only Office 365 and block everything else. I hope it won't create any problem when it goes live.
I like the way you mentioned every detail in the photos.
Thank you so much for your time and effort.
Regards.
-
3rd Party VPN
170 -
ACLs
91 -
Auto VPN
296 -
AWS
36 -
Azure
68 -
Client VPN
379 -
Firewall
848 -
iOS
1 -
Other
547 -
Wireless LAN MR
1