Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Re: MX Firewall Rules not applying consistantly
MX Firewall Rules not applying consistantly
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MX Firewall Rules not applying consistantly
Hi,
I have a 2 networks that seems to not apply Layer 3 Firewall Rules as expected.
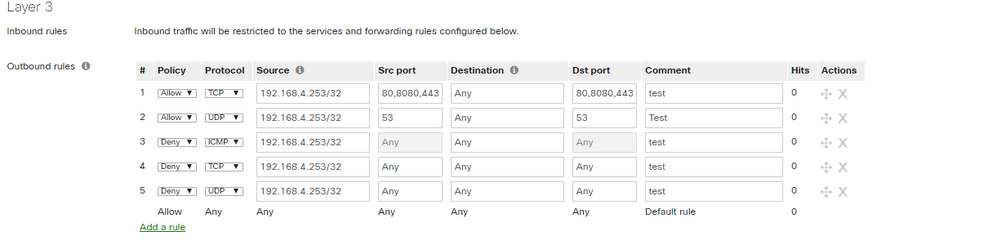
Below rule should allow internet browsing for IP 192.168.4.253 but all traffic is denied.
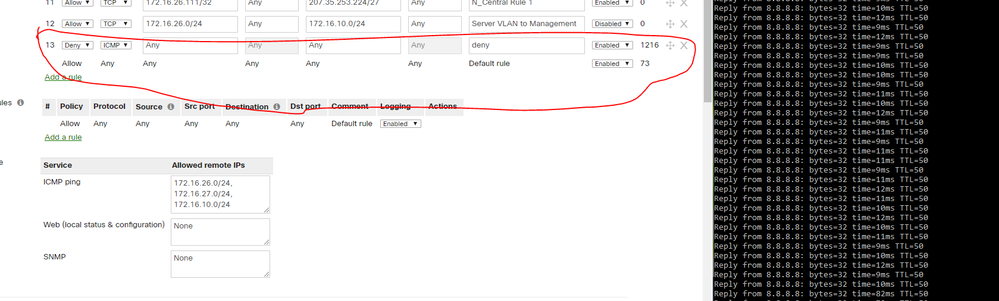
On another network I configured below rule to block all ICMP traffic for testing purposes but can still ping out of network. It shows that traffic is hitting the deny rule but can still ping through.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Regarding the first ruleset.
- You shouldn't specify source ports. Source ports are chosen randomly by the operating system. They will likely not be 80, 8080 or 443. So basically the 1st rule is being skipped.
- The second rule same thing, source port should not be specified so likely this rule is skipped again.
- The third rule blocks all pings. I assume this is working.
- Then the 4th and 5th rules will basically block all other TCP and UDP requests, so the skipping of the first and second rule likely result in the connections hitting this rule and being blocked.
Regarding your second problem. Are you sure the PC you're testing from is using that MX to go towards the internet? Any group policies that are overriding and giving it access?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you,
Sorted out the first one thank you.
I've double checked and there is no special group policy applying to the pc. All clients on network can ping out even though the rule is specified.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Good to hear.
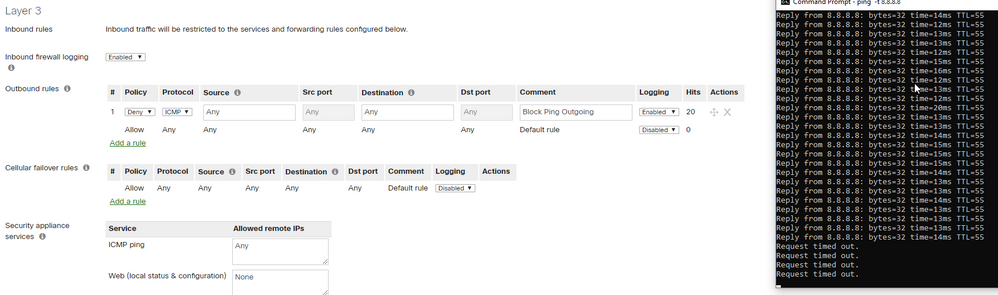
For the second problem. I tested out with the same rule and it works fine here:
Is it possible there's a rule higher up that allows the pings? The first applicable rule will take the decision.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Moved Rule to top and still allowing traffic.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can you check with traceroute whether the MX is actually in the path a packet takes?
Can you also remove the IP addresses in the "Allow Remote IPs" column for the "ICMP ping" service. I think those may be interfering as I believe the MX expects the addresses to be listed here to not be present on it's LAN subnets.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
One of the first things I checked. Can confirm that its routing via MX.
Removed the IP's from Allowed Remote IP's and still allowing ping to go through.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Tbh, then I don't know what's going on. It seems to me that they shouldn't be going through. As a last resort I'd probably try a packet capture on the WAN port of the MX to see that I actually see those pings going out to make sure we're not overlooking something. VPN software on the laptop may be causing the traffic to be encapsulated.
-
3rd Party VPN
171 -
ACLs
91 -
Auto VPN
298 -
AWS
36 -
Azure
70 -
Client VPN
381 -
Firewall
851 -
iOS
1 -
Other
549 -
Wireless LAN MR
1