Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Group Policy Blocked URL pattern with Whitelisted IP Addresses
Group Policy Blocked URL pattern with Whitelisted IP Addresses
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Group Policy Blocked URL pattern with Whitelisted IP Addresses
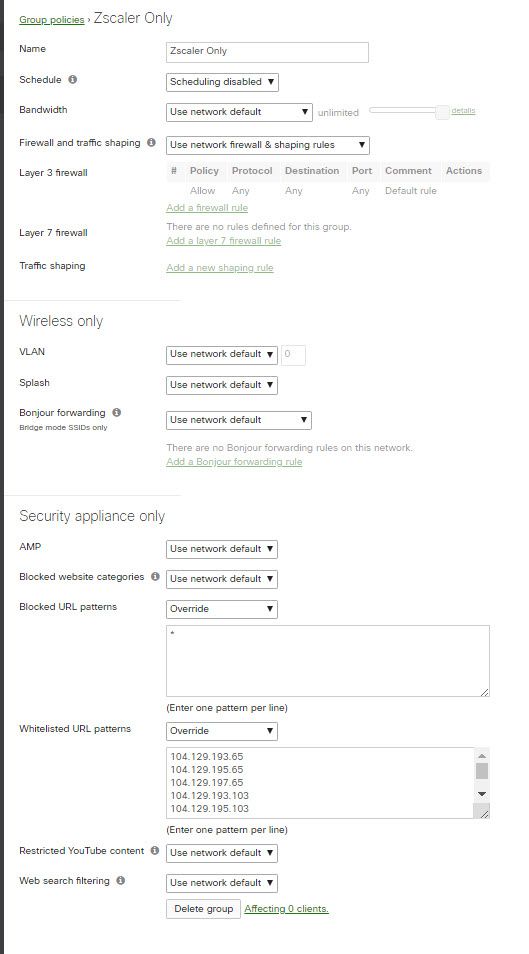
We use the Zscaler app on our desktops and we want to fall back to "block all" if Zscaler fails or is disabled. We tried to set up a group policy that limits outbound access to the Zscaler IP addresses.
We want to block all URL patterns and allow a list of IP addresses in the Whitelist. Is there a way to use CIDR IP addresses instead of URL patterns in the Whitelist.
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I've never looked into the Zscaler app before, but am i correct when I say that basically all your outgoing traffic gets tunneled to Zscaler via the app?
If only access to the IPs you listed is needed for that, why don't you use the L3 firewall to block all outgoing access except to those IPs? Seems to me that using the URL blocking feature is not meant for that?
Probably stating the obvious here but test on non-production first 🤣
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It looks like their are DNS names you can use instead of IP addresses.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the suggestion.
I will add zscaler.net to the whitelist and see if that works.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I've never looked into the Zscaler app before, but am i correct when I say that basically all your outgoing traffic gets tunneled to Zscaler via the app?
If only access to the IPs you listed is needed for that, why don't you use the L3 firewall to block all outgoing access except to those IPs? Seems to me that using the URL blocking feature is not meant for that?
Probably stating the obvious here but test on non-production first 🤣
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
My original assumption was faulty. I assumed that I would be able to block everything except for Zscaler traffic. This did not work. Even though the traffic is bound for Zscaler, it still gets blocked by the MX.
The Meraki firewall must still see the url and blocks it.
I think that BrechtSchamp is right. I would have to block traffic at the L3 firewall for this to work.
Thanks for the help.
-
3rd Party VPN
170 -
ACLs
91 -
Auto VPN
296 -
AWS
36 -
Azure
68 -
Client VPN
379 -
Firewall
849 -
iOS
1 -
Other
547 -
Wireless LAN MR
1