We're migrating to the Cisco Community on March 31. The Meraki Community will enter read-only mode starting on March 26 through March 31.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Configuring Active Directory Authentication
Configuring Active Directory Authentication
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Configuring Active Directory Authentication
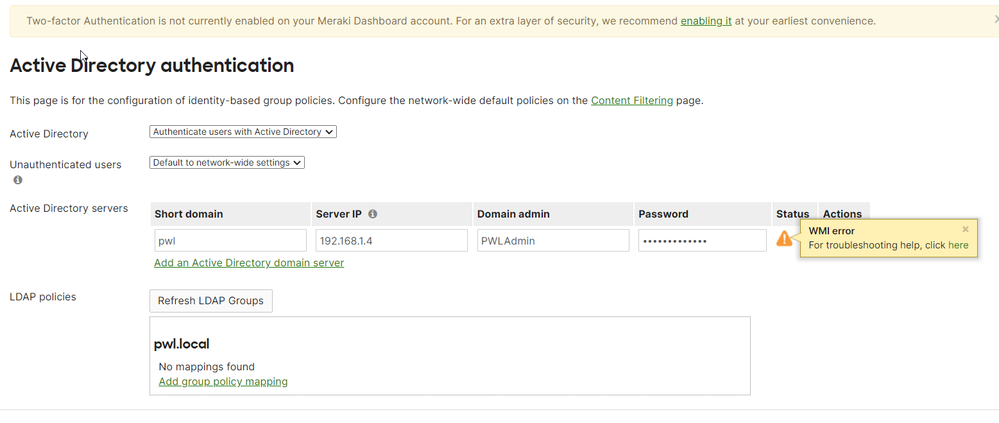
I am trying to configure AD Authentication on an MX67 with firmware 17.10.2 so I can have clients that connect to the Client VPN to authenticate via our on-prem Active Directory Server.
I have put in my correct AD information (shown below), but I keep getting the WMI error message. On the server in Event Viewer, I get this Event ID 10036:
The server-side authentication level policy does not allow the user PWL\PWLAdmin SID (S-1-5-21-2010977204-1741935109-2524261170-500) from address 192.168.1.1 to activate DCOM server. Please raise the activation authentication level at least to RPC_C_AUTHN_LEVEL_PKT_INTEGRITY in client application.
And I have tried to edit the permissions in dcomcnfg.exe to allow the DCOM Users group, but still get the WMI message and event viewer message shown here.
PWLAdmin is the default administrator on the server, just renamed. I have even tried a new user account that is a member of Domain Admins. Same situation.
I have made absolutely certain that the settings in the screenshot are correct for our on-prem AD server.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
There are a few steps you should take first:
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Which parts? In my previous research, it referred to installing a TLS Cert on the server, but the instructions are pretty vague on how to do that, as are the instructions in the link. Other search results I've found refer to installing IIS to generate a self-signed cert. But then what? I am not very "up" on generating and installing certs.
The server is on the same LAN as the Meraki and the Meraki can communicate with the AD server just fine.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Enable the Global Catalog Role on Each Domain Controller
In order for a Domain Controller to maintain the logon events used by the MX for user/group identification, it must be running the Global Catalog Role. As such, a required configuration step is to enable the Global Catalog Role for each Domain Controller that the MX will be polling.
Please refer to official Microsoft documentation for specific configuration steps.
Enable Security Auditing on Active Directory Domain Controllers
Explanation
When Active Directory Group Policy is enabled, the MX pulls a continuous stream of Security Events from Windows Active Directory Domain Controllers. Using Logon Events (540 and 4624) and Account Logon Events (672 and 4768) specifically, the MX can determine which domain users are logged into which domain computers and what the IP address of those computers are. This information is then coupled with the users Group Membership retrieved from an LDAP/TLS lookup and the IP address or MAC address of the computer learned via Cisco / Meraki client detection. By combining these pieces of information, the appropriate filtering policy can be applied transparently in real-time to each computer based on the currently logged on user. If Domain Controllers specified in Dashboard do not have Security Auditing enabled, the MX will not be able to associate users to computers transparently. To ensure that a Domain Controller is configured to audit successful Logon and Account Logon Events, enable this logging using the Default Domain Controller Policy or Local Computer Policy for Domain Controllers in your domain.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
For years all I needed in the username was the username without prefix of the domain with a slash:
domain\username after checking all the other fixes including deploying IIS on all domain controllers I added the domain\ prefix in my login credentials and received a green check-mark instead of orange or red failure.
Just in case someone else is having trouble.
Not sure if that is all what was needed but in the end that is what helped me.
Here is more info on the IIS server:WMI error - The Meraki Community
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
306 -
AWS
36 -
Azure
70 -
Client VPN
383 -
Firewall
868 -
iOS
1 -
Other
557 -
Wireless LAN MR
1