Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Client VPN Issue
Client VPN Issue
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Client VPN Issue
Hi Forum,
I have a customer that has a MX Device behind a NAT Router and the client wants to have the Client VPN feature enabled so we are busy testing this for him using the Meraki Cloud Authentication. We are not able to configure the NAT Router in Bridge mode but we have configured it to forward UDP500 and UDP4500 ports to the MX device.
Before we configured the router to forward UDP 500 and UDP 4500 to the MX Device, we were not able to connect and we were receiving an L2TP Error message on the Windows 10 device. We were also not seeing any events in the Event Log on the MX Device. After forwarding these ports to the MX Device, we are now seeing the events in the Event Log and it seems as if the MX device is completing the connection but we still get a failed connection on the Windows 10 device ("The connection was terminated by the remote compute before it could be completed")
Below is an output of the events in the MX Event Log:
| Jun 29 15:57:26 | Non-Meraki / Client VPN negotiation | msg: <l2tp-over-ipsec-1|5> deleting IKE_SA l2tp-over-ipsec-1[5] between 192.168.8.101[192.168.8.101]...169.159.156.42[10.0.2.15] | |
| Jun 29 15:57:26 | Non-Meraki / Client VPN negotiation | msg: <l2tp-over-ipsec-1|5> closing CHILD_SA net-1{17} with SPIs c3e94349(inbound) (825 bytes) a8824164(outbound) (721 bytes) and TS 192.168.8.101/32[udp/l2f] === 169.159.156.42/32[udp/l2f] | |
| Jun 29 15:57:25 | Non-Meraki / Client VPN negotiation | msg: <l2tp-over-ipsec-1|5> CHILD_SA net-1{17} established with SPIs c3e94349(inbound) a8824164(outbound) and TS 192.168.8.101/32[udp/l2f] === 169.159.156.42/32[udp/l2f] | |
| Jun 29 15:57:24 | Non-Meraki / Client VPN negotiation | msg: <l2tp-over-ipsec-1|5> IKE_SA l2tp-over-ipsec-1[5] established between 192.168.8.101[192.168.8.101]...169.159.156.42[10.0.2.15] | |
| Jun 29 15:53:32 | Non-Meraki / Client VPN negotiation | msg: <l2tp-over-ipsec-1|3> deleting IKE_SA l2tp-over-ipsec-1[3] between 192.168.8.101[192.168.8.101]...169.159.156.42[10.0.2.15] | |
| Jun 29 15:53:32 | Non-Meraki / Client VPN negotiation | msg: <l2tp-over-ipsec-1|3> closing CHILD_SA net-1{16} with SPIs c8d42dee(inbound) (825 bytes) a67b2806(outbound) (721 bytes) and TS 192.168.8.101/32[udp/l2f] === 169.159.156.42/32[udp/l2f] | |
| Jun 29 15:53:31 | Non-Meraki / Client VPN negotiation | msg: <l2tp-over-ipsec-1|3> CHILD_SA net-1{16} established with SPIs c8d42dee(inbound) a67b2806(outbound) and TS 192.168.8.101/32[udp/l2f] === 169.159.156.42/32[udp/l2f] | |
| Jun 29 15:53:30 | Non-Meraki / Client VPN negotiation | msg: <l2tp-over-ipsec-1|3> IKE_SA l2tp-over-ipsec-1[3] established between 192.168.8.101[192.168.8.101]...169.159.156.42[10.0.2.15] |
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Steven
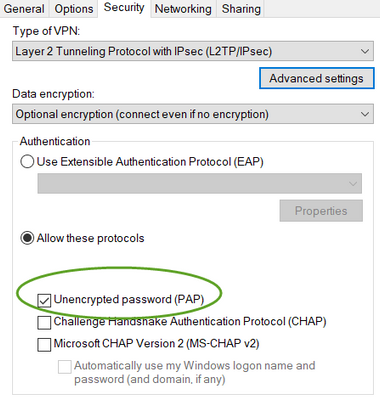
Try this ; check the PAP on windows !
https://documentation.meraki.com/MX/Client_VPN/Client_VPN_OS_Configuration#Windows_10
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That worked for me thanks Manjinder.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Not sure if this helps, we had similar issues on Windows 10 Native VPN client. The option I believe we had to set was to make sure all traffic was routed through the VPN (i.e no split tunneling).
Thanks
Sarvjit
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You'll will need to configure the AssumeUDPEncapsulationContextOnSendRule registry entry on Windows 10 machines to allow it to work through NAT.
The easy way - use my online tool to create a PowerShell script to create the VPN connection for it. It'll set all the other tricky stuff so it is most likely to work.
https://www.ifm.net.nz/cookbooks/meraki-client-vpn.html
The other option is to use the MX 16.x code and buy some AnyConnect licences (cheap). This uses TLS, and works automatically in cases like this. After upgrading to 16.x you can test out AnyConnect before buying the licences.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi PhilipDAth
I have already configured this option - AssumeUDPEncapsulationContextOnSendRule - and it does not work. I will try your online tool and see if that helps. I will keep you posted on my progress
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You wouldn't happen to have a site-site VPN connected as well would you? I am running into the exact same issue that you have. However, I have a site-site VPN connected, and found that when I disable VPN availability for all the VLANs I configured it for, I'm able to make the client VPN connection. Same goes for when I just take the site-site VPN down. I'm probably going to have to call support to help figure out why this is the case.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
For me it worked 🙂
I set the AssumeUDPEncapsulationContextOnSendRule value to 2 as I was trying to connect from within the internal network to a remote server that is configured with a site-to-site VPN to my network.
It took me hours but finally is working 😉
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have spent significant amount of time investigating this. It is a problem with Windows using VPN with NAT-T.
If you use a MacOS computer, you will be able to connect immediately.
Setting the registry key was a hit or miss for me:
The real solution for me was actually updating Windows to the very latest patch. Along the way Windows themselves must have noticed an issues and one of the patches fixed it.
Make sure to delete the VPN connection and recreate it.
-
3rd Party VPN
170 -
ACLs
91 -
Auto VPN
296 -
AWS
36 -
Azure
68 -
Client VPN
380 -
Firewall
850 -
iOS
1 -
Other
549 -
Wireless LAN MR
1