- Technical Forums
- :
- Security & SD-WAN
- :
- Cisco jabber with MX
Cisco jabber with MX
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Cisco jabber with MX
Hello,
We have a case that need is to allow Cisco Jabber to be accessible from out side of the network. For that, we’re following the cisco guide.
the idea is to allow Jabber clients register to the on premise cisco call manager.
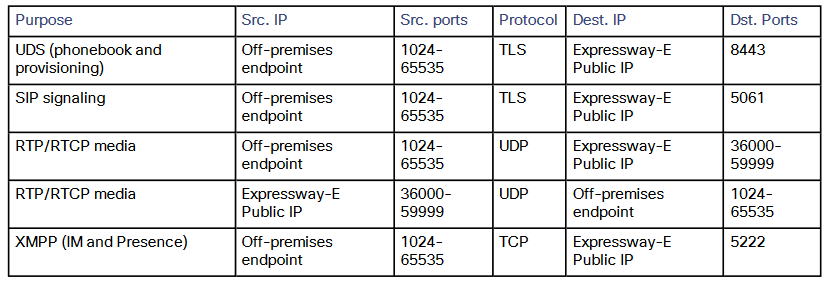
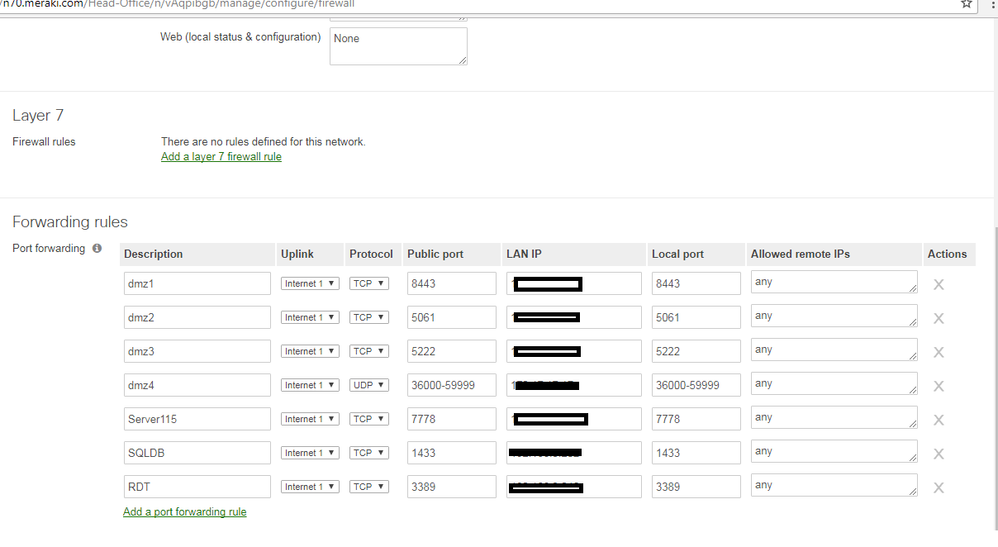
The optimum scenario (in other firewalls) , is to configure the Edge Expressway server as a DMZ client behind the firewall so that whenever the public IP of the firewalls is requested, it’s forwarded to the DMZ client (the edge expressway server). Unfortunately, the Meraki MX does not have a ready to use DMZ client straight config. So we need to configure port forwarding as per the attached requirements from Cisco.
When we try to do it, the MX refuse to save and says the source ports and the dist. Ports should be in the same range!
How do you suggest we resolve this issue knowing that the ISP only provided one public IP (used for the MX wan port) with no extra spare public IP to be used.
Appreciate your inputs...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I think the problem you're experiencing is that in the "Public port" you're putting in the "Source Port". The "Public Port" is actually the "Destination Port" of the traffic hitting the "Public IP" of the MX. Heres an idea, e.g for the last rule; You'll just then have to follow the same concept for all the other required rules.
Description - Uplink x - Protocol - Public port - LAN IP - Local Ports - Allowed remote IP's
XMPP - Uplink 1 - TCP - 522 - LAN IP of Edge Expressway - 522 - Public IP of remote hosts (If a variety of ranges you could use any)
Effectively if you allow "any" this will allow all incoming traffic with the destination port 522 to be forwarded to the Edge Expressway. Try and limit it to the remote locations via public IP's.
Found this helpful? Give me some Kudos! (click on the little up-arrow below)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Also note that the second to last rule for udp/1024-65535 is not actually for the server so there is nothing to enter.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
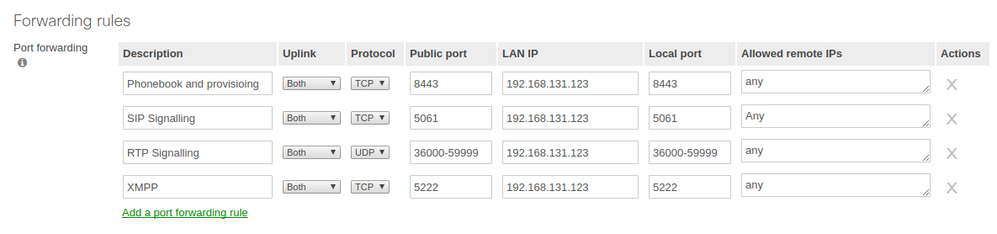
I believe your forwarding rules (under Security Appliance/Firewall) should look something like this (where 192.168.131.123 is your server):
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@PhilipDAth thanks .. We did as per the picture.. Jabber registered and able to make calls but Not able to hear the other end ( & the other end cant hear us as well) .. are there any other RTP ports needed for this or other ports to be forwarded?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Wondering if this was ever resolved?
-
3rd Party VPN
170 -
ACLs
101 -
Auto VPN
314 -
AWS
39 -
Azure
71 -
Client VPN
431 -
Firewall
715 -
Other
594