We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Anyconnect with Radius (Multifactor)
Anyconnect with Radius (Multifactor)
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Anyconnect with Radius (Multifactor)
Hi,
I'm stuck and I don't know if my configuration is wrong or if this is just a limitation of how the interaction between Radius/Meraki/Anyconnect works at the moment.
Currently I have my old Cisco ASA5500 series Firewall set up, with Anyconnect using DAP profiles and Multifactor Authentication (Entrust) running on a Radius server. It works perfect and is easy to use.
But my Firewalls are getting old and we have decided to move on and have chosen the Meraki as our new platform.
So far so good. I got Anyconnect up and running with my Radius server, and I can filter the logins with which group a user is a member of (from the AD) and then throw that back to the Meraki, so I make sure the right "Group Policy" is deployed (almost like DAP).
The problem start, when I introduce my "Entrust" solution, which is our Multifactor, running as a piece of software on the Radius server. The setup is exactly the same as when it runs with the ASA, but when I try to log in, the authentication prompt tells me "Login failed." after I have typed in my user credentials. But what really happens behind the scene is, the username and password was validated successful and now the Anyconnect client waits for the "Challenge/Response". If I then type in the OTP received (Text message), Anyconnect will tell me that "You have successfully connected to client VPN".
To me it looks like the Anyconnect and Meraki are having some issues doing the "Challenge/Response" part, which works fine on the ASA. Same configuration on the NPS more or less.
I've been in contact with Entrust, which ran through the logs and everything seems to be right on their end. It sees the Radius authentication, it then fires the Challenge/Response where I receive the text message and finally it accepts the response and verification is successful.
Do any of you have some similar setup, or perhaps know if this is a limitation of how Anyconnect is working on Meraki as if now?
Thank you.
- Labels:
-
Client VPN
-
Other
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Take a look at this: https://documentation.meraki.com/MX/Client_VPN/AnyConnect_on_the_MX_Appliance/Authentication
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, but looking at the integration it looks like this is being done in the Cloud and the integration with my Radius servers and policies will then no longer be in place?
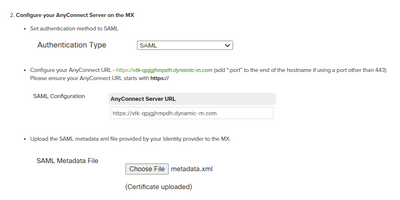
But, if I move ahead with the SAML integration, how do I then get the SAML displayed on my MX?
I can only under "Anyconnect" see the following authentication types: RADIUS, Meraki Cloud Authentication and Active Directory".
My appliance is running:
Do I miss something in the steps somewhere?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
As far as I know you need to ask Meraki support to enable it for you:
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Have you set the RADIUS Timeout on the Anyconnect Page to something different than the default 3 seconds? Perhaps set it to 60 seconds?
Like what you see? - Give a Kudo ## Did it answer your question? - Mark it as a Solution 🙂
All code examples are provided as is. Responsibility for Code execution lies solely your own.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hey,
Yes I have tried with 30 seconds and also 60 seconds, but no difference. I'm sure it must be me doing something wrong, but I just can't figure out what it is, neither could the Entrust technician 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I can't say how it is with Entrust, but I've just got it working with Okta and their RADIUS Agent.
Like what you see? - Give a Kudo ## Did it answer your question? - Mark it as a Solution 🙂
All code examples are provided as is. Responsibility for Code execution lies solely your own.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
But is OKTA also able to use RSA Tokens / SMS Tokens / Grid Cards and so on?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Okta can use SMS passcodes, Push Notification Apps etc, as well as a range of third party MFA vendors such as DUO. I don't know if they also support Entrust.
Like what you see? - Give a Kudo ## Did it answer your question? - Mark it as a Solution 🙂
All code examples are provided as is. Responsibility for Code execution lies solely your own.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'd be willing to bet what you're describing might run into the compatibility issues described here: https://documentation.meraki.com/MX/Client_VPN/AnyConnect_on_the_MX_Appliance/Authentication#Multi-F...
If the MFA request is coming in the form of an additional access-challenge packet that has an attribute-value pair prompting users to enter an OTP, that's not currently supported, and I don't know of a timeline in which it will be.
The only way MFA is supported right now is if the server sends out a prompt directly to your users (e.g. a push notification) and then sends an access-accept to the MX after the OTP has been entered by them.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ouch, you might be right :(. Wonder if this is a thing that will be worked on or just not supported.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I can't comment on any sort of roadmaps as a whole unfortunately, but if you want to try and confirm this is the problem, take a pcap on your MX and look at the RADIUS traffic. If the last thing you see is an access-challenge packet containing the AVP I described above, yeah that's confirmation on the problem.
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
305 -
AWS
36 -
Azure
70 -
Client VPN
382 -
Firewall
866 -
iOS
1 -
Other
556 -
Wireless LAN MR
1