Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Anyconnect auth against ISE with Azure MFA
Anyconnect auth against ISE with Azure MFA
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Anyconnect auth against ISE with Azure MFA
Hi all,
So today we have a Cisco ASA solution running that is EOL and now we need to migrate to our new Meraki Anyconnect solution.
Today on our ASA solution we are running Radius against ISE that connect to Azure MFA so you get the 2 factor to run, and that works perfect ISE has some prebuild in function (Cisco-VPN3000/ASA features) but now comes the issue for me.
So I can make a policy in ISE that allows my user to login with user auth, without MFA but that is not enough, so how to create a policy that trigger this condition for my MFA. The condition for Cisco-VPN3000 is not working for Meraki, so what has people done here to get this work?
Looking forward to hear what people has done here for getting 2 factor to work through ISE with MFA.
Frank
LinkedIn - Twitter
Found this helpful? Give me some Kudos! Much Thanks
Solved! Go to solution.
- Labels:
-
Client VPN
-
Other
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Unless you are using ISE for other things - you probably don't need it.
Most people SAML authentication directly against things like Azure AD (you can SAML authenticate against other MFA providers).
https://documentation.meraki.com/MX/Client_VPN/AnyConnect_on_the_MX_Appliance/Authentication
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Maybe It can help you:
https://community.cisco.com/t5/security-knowledge-base/notes-on-azure-ad-as-saml-idp/ta-p/3644255
https://documentation.meraki.com/MX/Client_VPN/AnyConnect_on_the_MX_Appliance/Authentication
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the links, but not really what I am looking for here.
It might be that I need to redo something here to get MFA for Azure to work.
The flow today is the following:
ASA - Cisco ISE - Azure MFA
- The radius request is sent to my Cisco ISE, that handles the request to our Azure MFA setup.
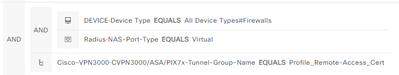
The condition here in ISE and my policy looks like this:
Here use the Cisco-VPN3000/ASA/PIX7x-Tunnel-Group that the ASA sends to ISE to trig the Azure MFA function, but what is Meraki sending??
I need to trig the same function inside ISE here. but what is Meraki using here??
So it might be more the ISE condition I need help with, because Meraki is very simple here on what you can setup in the dashboard. 🙂
So is hoping somebody else has setup Anyconnect with ISE and some MFA. 😄
Frank
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Unless you are using ISE for other things - you probably don't need it.
Most people SAML authentication directly against things like Azure AD (you can SAML authenticate against other MFA providers).
https://documentation.meraki.com/MX/Client_VPN/AnyConnect_on_the_MX_Appliance/Authentication
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Philip
Year I use ISE for a lot of things, but looking more into SAML it might be a idea to use Azure AD..... What option does this give you here? Can you utilize all the feature that there are in Azure AD like, postering, compliance check etc.?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hmm, The tunnel-group thing is a specific configuration construct in ASA appliances.
You use that construct in an ASA to differentiate between authentication methods/aaa servers.
I don't think you can use this distinction on Meraki since you can only select 1 authentication method so you will have to change up your matching criteria.
The more difficult thing is to have a distinction between internal employees and external contractors. You'll need to have them inside your AD domain under a specific group.
-
3rd Party VPN
172 -
ACLs
91 -
Auto VPN
301 -
AWS
36 -
Azure
70 -
Client VPN
381 -
Firewall
856 -
iOS
1 -
Other
552 -
Wireless LAN MR
1