Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- AnyConnect with Azure AD SAML - User's get "Can't reach this page"
AnyConnect with Azure AD SAML - User's get "Can't reach this page"
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
AnyConnect with Azure AD SAML - User's get "Can't reach this page"
Firmware 17.8 (same issues with 16.16)
Set up AnyConnect Azure AD SAML. One user authenticates successfully and receives 'Can't reach this page' in the Cisco AnyConnect Login box after providing MFA.
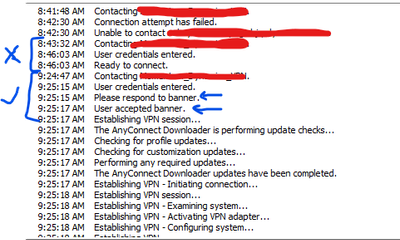
When I test with my admin account, this first time it hangs after successful MFA and finally gives a 'CSRF token failed' message. Then each time I attempt afterward it will successfully connect. Here is the AnyConnect log showing the first failed attempt and the subsequent successful attempt:
I notice the first time, I don't see the banner message. Both users testing (including myself) are in the Azure AD enterprise app group.
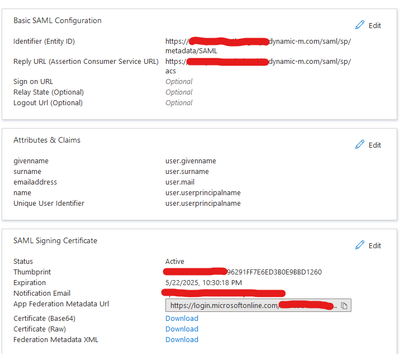
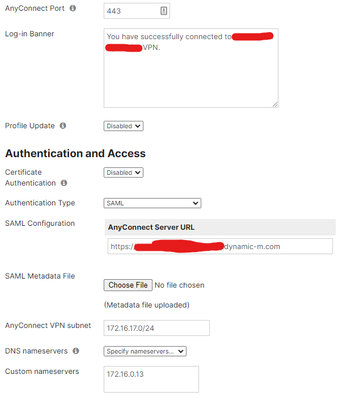
My AnyConnect / Azure AD settings:
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Update: After speaking with Microsoft and Meraki support and getting back to square one, I decided to try changing the primary WAN from 2 (Verizon) to 1 (Comcast). This apparently worked. My connection worked every time, and a user who never had a successful connection worked every time as well. There was/is some loss (and I mean 1-3% every so often on the Verizon circuit), so maybe that's part of the issue. We are going to contact Verizon to see if they can check the circuit/signal.
Another note: Make sure your CA policies are in good order. I found that a user was being checked by the wrong CA policy first, and that policy was causing issues. Make sure to exclude AnyConnect from all other policies so that only the appropriate policy applies to enforce MFA.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That is unusual. With an error like CSRF it is usually broken everytime.
Are running a current stable firmware release on the MX?
As a matter of interest, does the MX have a public IP address on it?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for response. Current version is 17.8 which is seemingly stable. Yes, there is a static public IP on it. In fact there are two static IPs (two ISPs) that are active. Maybe that is an issue? Perhaps I should configure one as backup.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It seems to work on every other connection. I've also run a packet capture and I don't see any data on the failed attempts. Could this be some Azure AD response requirement that is not showing up correctly, and then ultimately times out?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Update: After speaking with Microsoft and Meraki support and getting back to square one, I decided to try changing the primary WAN from 2 (Verizon) to 1 (Comcast). This apparently worked. My connection worked every time, and a user who never had a successful connection worked every time as well. There was/is some loss (and I mean 1-3% every so often on the Verizon circuit), so maybe that's part of the issue. We are going to contact Verizon to see if they can check the circuit/signal.
Another note: Make sure your CA policies are in good order. I found that a user was being checked by the wrong CA policy first, and that policy was causing issues. Make sure to exclude AnyConnect from all other policies so that only the appropriate policy applies to enforce MFA.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I will mark this as acceptable. We are talking with Verizon at this point to discuss the WAN connection.
In short, if you see what seem to be random issues as described above:
1. Test with the other WAN (if you use two WANs in load balance or fail-over mode
2. Make sure your AnyConnect Enterprise App is only tied to ONE Conditional Access policy
-
3rd Party VPN
165 -
ACLs
90 -
Auto VPN
290 -
AWS
36 -
Azure
66 -
Client VPN
368 -
Firewall
835 -
iOS
1 -
Other
540 -
Wireless LAN MR
1