We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Re: AnyConnect and Local LAN access
AnyConnect and Local LAN access
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
AnyConnect and Local LAN access
Hi
I'm facing a strange issue when I try to access my Local LAN when connected with AnyConnect to my Corporate MX (or vMX).
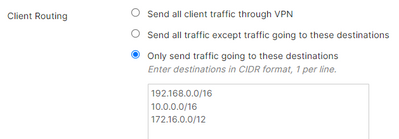
I've set the AnyConnect Server to send traffic over the VPN only to specific destinations.
I've deployed a Profile that allow LocalLAN access but it seems it works only in Full Tunnel mode.
Does anyone get same issue ?
Thanks
Marco
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
AT least with legacy Cisco gear you had to exclude 0.0.0.0/32 from your tunnel.
Here you tell Anyconnect to tunnel everything RFC1918 to your VPN headend, so basically it simply is doing what you're telling it to do.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for you reply
unfortunately I cannot find a place where I can exclude 0.0.0.0/32 from Tunnel
the option is available only in Full Tunnel Mode
If you can find where, please let me know.
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This will be because your local LAN subnet falls within one of the subnets above - which you have told AnyConnect to forcibly send to the MX. If you make the scopes narrower so it doesn't include your local subnet it will work.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
As @PhilipDAth says, your local LAN is likely to be 192.168.0.0/24 or similar and covered by your forced routing. You need to remove the network that overlaps and have more specific ones that exclude it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks to all.
unfortunately I cannot control Local LAN Client settings and is too complicated to manage exclusions/nclusions.
I need to find another solution
Thanks again
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@MarcoBri don't route 192.168.0.0/16 over the VPN. If you are using any of it in the corporate network then re-IP those sites. A corporate network should not use 192.168 networks unless you never intend remote access from people's homes.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Unfortunately I cannot re-IP hundreds of networks.
those networks were assigned before allowing remote access
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You don't need to. Can you not extract a list of the 192.168.0.0/16 subnets in use in the network?
The biggest ones to avoid are 192.168.0.0/24 and 192.168.1.0/24.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I already have the list but are more than 300, most of them subnetted , including 192.168.0.0/24 and 192.168.1.0/24.
I've realized that someone is using 192.168.80.0/24 at home !
A possible solution could be to send ALL traffic through the VPN and exclude 0.0.0.0/32.
In this way I can use my local LAN, any network address.
the problem is that if I terminate the AnyConnect VPN to a vMX, Internet Access is lo longer allowed.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I would look at whether you need to provide VPN access to 192.168.0.0/23. Perhaps there are no servers that need remote access. Problem solved.
Next, I would look into renumbering just those two networks. You could even create a new VLAN at those sites, and renumber just the individual servers that need remote access and leave everything else "as is".
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Lol, @PhilipDAth I had a bite to eat mid reply and just wrote almost the same
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If you don't want to re-IP all 192.168 networks, then I'd at least move the corporate 192.168.0.n and 192.168.1.n networks to new IP ranges and then most home users will be okay. Home users on other IP ranges have probably chosen a different range so can change it back it they want local access.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I use 10.238.0.0/24 at home, so I worked the subnets around that:
10.224.0.0/13
10.232.0.0/14
10.236.0.0/15
10.238.1.0/24
10.238.2.0/23
I've given it time, connected twice, have "Allow local LAN" access enabled in the client, yet a route still gets added with higher priority pointing my subnet to the Anyconnect.
10.238.0.0 255.255.255.0 On-link 10.238.0.126 306
10.238.0.0 255.255.255.0 On-link 10.238.3.103 2
10.238.0.1 255.255.255.255 On-link 10.238.0.126 51
I could forcibly create a route with a higher priority, but wondering why its doing this at all. Am I missing something?
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
305 -
AWS
36 -
Azure
70 -
Client VPN
382 -
Firewall
866 -
iOS
1 -
Other
557 -
Wireless LAN MR
1