- Technical Forums
- :
- Security & SD-WAN
- :
- Allowing Inbound Traffic on MX
Allowing Inbound Traffic on MX
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Allowing Inbound Traffic on MX
I have an MX deployed which uses a MPLS link to connect to the HQ. The same link is used for providing internet to the MX and the subnet behind MX, using the internet link at HQ. NAT is disabled on MX. All NAT takes places on the HQ border router. Internet is working fine but I have issue with traffic between HQ and the Branch MX.
Although I can reach HQ LAN subnets using the MPLS link but it doesn't work in the reverse direction. I cannot access Meraki LAN subnets when sourced from HQ LAN since the MPLS link terminates on the Internet port of MX. Can the MX use one of it LAN ports to provide internet access to the MX itself?
I have multiple HQ LAN subnets that need to communicated with multiple MX LAN subnet. Is there a way to allow inbound traffic where I have the MPLS link connected on the Internet port of MX?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I haven't used this configuration - but are you sure you have NO-NAT mode enabled?
You would make life simpler if you deploy an MX as a VPN concentrator in your HQ and use AutoVPN over MPLS to provide the connectivity.
https://documentation.meraki.com/MX/Site-to-site_VPN/Configuring_Site-to-site_VPN_over_MPLS
Then you don't need NO-NAT mode.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
No-NAT feature is available in OS 15.15 and yes we have it enabled on the WAN link.
We don't have a MX in the HQ. Currently only the branch has a MX hence AutoVPN is not a possible.
Secondly i cannot create a IPSec VPN with the HQ since the link between HQ and Branch is not direct. I wanted to keep the details simple so didn't mention this earlier.
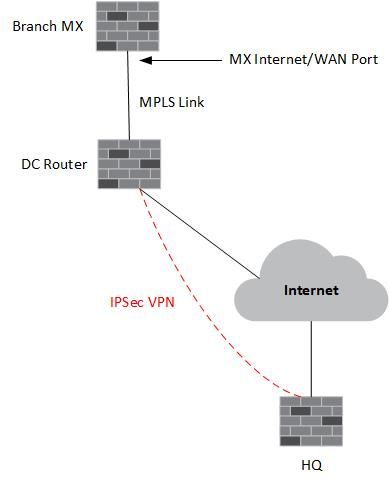
The network connectivity is as follows:
The branch MX has MPLS link going to a Router in a DC. The DC router has Internet connection. This internet link is used for providing internet access to MX and its LAN subnet. The internet link on DC router is also used to establish an IPSec VPN with the HQ.
Now if traffic is initiation from HQ LAN, it reaches MX WAN interface but is then dropped because by default inbound connections are not allowed on MX. Is there a way to allow these?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Why do you have an MX at the branch if you want to just let all traffic in and out without NAT? What is it you want to achieve?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hey SohaibA,
If this is obvious forgive me but just in case....
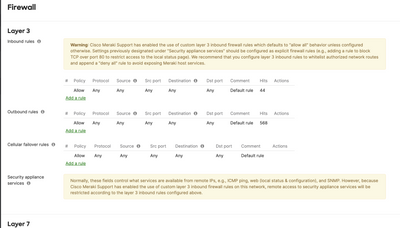
Just because NAT is disabled doesn't mean the firewall is. You still have to explicitly permit traffic from your HQ subnets into your MX's LANs. Try throwing some permit rules in there and seeing if that resolves your issue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I know this is old, but you have to call Meraki and have them enable the inbound firewall rules.
-
3rd Party VPN
170 -
ACLs
101 -
Auto VPN
314 -
AWS
39 -
Azure
71 -
Client VPN
431 -
Firewall
715 -
Other
594