My name is Robert Kremnitzer and I have been in the IT industry for a little over 5 years. I started as a Help Desk Tech and have gone from Systems Administration to Network Engineering and Security. I went from not touching anything in networking to, if it has a Ethernet port or is connecting wireless, it is in my to-do list.
We originally had Cisco WLCs and Office Extends setup prior to my arrival to allow users to work remotely. We also introduced Cisco ISE to allow us to utilize security best practices. Unfortunately at the time, we couldn't provide 802.1x and PoE to our remote workers. This forced us to be ill-secured at our employees homes and we had to include large PoE injectors to power the phones these employees needed. Now with the use of the Meraki Z3 and MX65W appliances, we are able to provide secure remote VPN access with 802.1x security and PoE utilization.
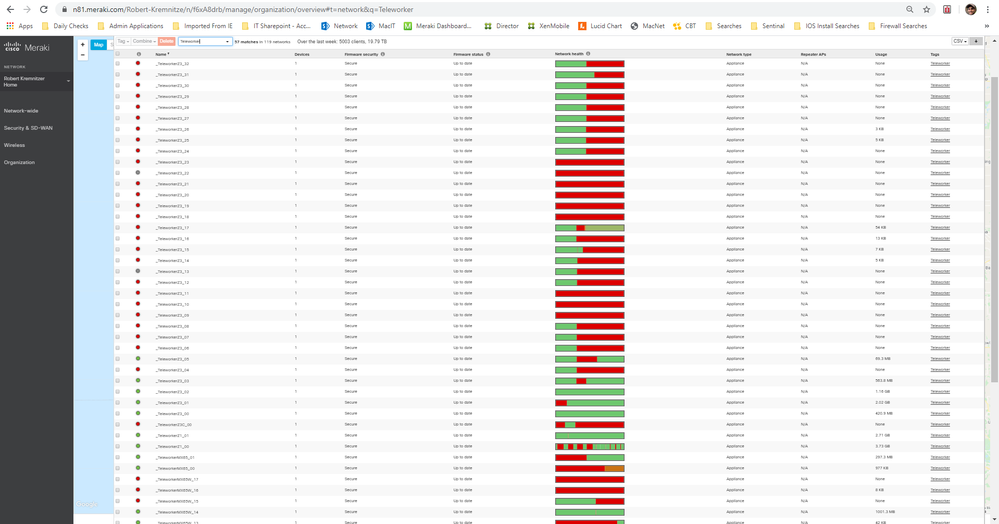
Within this last couple weeks, the COVID-19 coronavirus has caused us, much like the rest of the world, to ramp up our Teleworker/VPN users exponentially. Because of this exponential need, we had a huge influx of work-from-home/teleworker requests and needs. Thanks to Meraki's zero-touch deployment, we were able to build and deploy 57 networks within a couple hours. The Copy Configuration feature when building new networks was extremely helpful and made creating the networks, just a few clicks rather than rebuilding the entire network each time. Due to our distribution center's high volume requests in Z3 appliances, we were able to create these networks before we even had the equipment. Once the equipment arrived, we added it to the network, powered it up, and connected it to the internet. That was it! From there it was ready to deploy to our users.
Certain network custom configurations make using configuration templates not ideal. If we were able to utilize this feature, then even less work would have been required to deploy these networks. What did help me was the use of the Meraki API integration and the Meraki API Python SDK.
https://developer.cisco.com/meraki/api/#/python/getting-started
Once I built the python script, I was able to do everything I needed to build a network in a few lines of code and only handful of variables. This cut my deployment time in half!
The ramp of WFH/Teleworker needs will only increase from here over the next couple weeks and will most likely push our work force into a more remote work environment "norm". Meraki's simple zero-touch deployment, Auto-VPN ease of use connectivity, and the API integration have allowed us to be ready and make this current project another day's work rather than a nightmare.