- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Inbound Firewall Rules please
Inbound Firewall Rules please
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Inbound Firewall Rules please
Has anyone had any grief with not being able to create inbound firewall rules.
I personally have found this difficult especially coming from more traditional firewalls. It is especially frustrating today as i have clients utilizing our spam filter. and I've noticed a rogue "trying" to utilize it as a SMTP relay. (Immediately my first reaction is to block that specific IP on the firewall coming inbound to stop anymore packets from reaching the Spam filter. However Meraki does not permit this...) Or does it?
Ive created an outbound rule and regardless of whether its hitting or not my spam filter wont respond back but it doesn't stop the logs from appearing of the device trying to connect..
Has anyone heard if Meraki will be allowing the use of inbound rules now in or in future. What is stopping them today is it just due to all the potential extra management work it could cause
Certified Meraki Networking Associate
Kudo this if it helped! 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
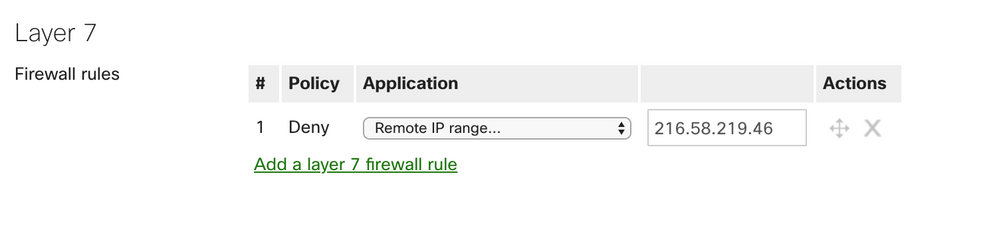
You could utilize the layer 7 firewall rules to block individual hostnames or IP(s). Is that what you are looking for?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
already had this as well. Sorry forgot to mention it. and i actually believe the layer 7 is still for outbound only as i can see the rogue device still hitting my spam filter. But i can see responses from my spam filter being blocked.
Certified Meraki Networking Associate
Kudo this if it helped! 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Meraki has an odd design philosophy, and maybe it is a greater network design philosophy of blocking as close to the destination device as possible.
In your case, blocking outgoing traffic to that IP would achieve the same result as blocking incoming traffic from that IP. But I agree, it is seemingly less secure since the traffic would reach the destination server and just not get returned.
Begs the question, what if the traffic is malicious or malformed. If that is the case I wouldn't even want the traffic getting to my server so blocking incoming would be most ideal.
If this was helpful click the Kudo button below
If my reply solved your issue, please mark it as a solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
exactly my concern!
Certified Meraki Networking Associate
Kudo this if it helped! 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@NSGuru @Adam Sorry to interrupt, but are you guys sure adding an outbound rule stops return traffic? That's not generally the way _stateful_ firewalls work... If traffic is permitted in one direction the return traffic is allowed regardless of configured ACL's in the return direction. If the MX works that way then that is counter to my expectations...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@jdsilva earlier after setting the rule on L7 and outbound i believe that it was blocking the traffic after i built the rule. Im watching it again now though and i see no packets hitting that rule now.... Luckily i have IP reputation turned on for my Spam Filter so it knows the IP is malicious and blacklisted. But the logs are piling up because i cant get my meraki firewall to block this on the front end.
Certified Meraki Networking Associate
Kudo this if it helped! 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@jdsilva I do want to redact my previous statement. I had forgotten that i built a group policy specifically for this clien(Spam Filter) I created the rule in the group policy it stopped sending or receiving from the blacklisted public IP.... and began sending through as another public IP. So now im working through stopping the malicious attacks in general.
Its hard to lock down SMTP when you are an MSP and your clients are utilizing it as a relay.
Certified Meraki Networking Associate
Kudo this if it helped! 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@NSGuru Ahh, OK then I would be confident return traffic is blocked. The GP L3 rules are stateless so they should be blocking that absolutely.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@NSGuru give Meraki Support a ring and ask about running the No-NAT, still a beta feature they can enable for you if it fits with your network design, and you can have configurable inbound firewall rules as well as make the MX more like a routing device without NATting on the uplink/WAN. Just like you have outbound rules to filter traffic from the LAN side towards the WAN/Internet or other VLANs for example, you can also have inbound rules to filter traffic coming from the WAN/Internet inbound with the same ability to specify protocol, source and destination addresses and port numbers.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
OK, confirmed. A Layer 3 outbound firewall rule does not block the return traffic to an inbound initiated flow.
Good. I can sleep easy at night again 🙂