Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Full-Stack & Network-Wide
- :
- Re: How safe to use VLAN 1 if it's not spannning or any device on it
How safe to use VLAN 1 if it's not spannning or any device on it
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How safe to use VLAN 1 if it's not spannning or any device on it
Hi Guys,
I have a question about the best practice around not using VLAN 1. I have VLAN 1 untagged in all trunks between MX and switches with the following.
* Do not have any devices.
* Don't have any DHCP configured.
* Don't have any VLAN interface created.
* VLAN 1 is not spanning anywhere except in these trunk ports between MX and switches
* Don't have any management traffic (Have separate VLAN for that)
* None of the edge ports contain VLAN 1
I have run packet capture with this design then I run another one using VLAN 5 same scenario, since the untagged VLAN is untagged I couldn't see any difference from VLAN 1 to VLAN 5.
Should I worry about anything related to security here? , Let me know if I am missing anything.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Not using VLAN1 is just a good practice recommendation as it is the default VLAN of any switch, but it does not mean that it cannot be used or that network security is at risk. Security goes much further than a simple VLAN.
If possible, avoid using it, but if you do, that's fine, it's not the end of the world.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@alemabrahao Thanks for your reply, do you know any list of security problems that might occur if I used VLAN 1? I am just curious to know the wisdom behind it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Unfortunately not, but you can Google it and analyze by your self.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The main reasons vlan 1 is considered a potential security risk is because it is the default vlan on switches.
This means that if you have any enabled and unconfigured ports on a switch, someone can plug in with immediate access to vlan 1.
Additionally vlan 1 is used to exchange control plane data for some protocols (especially legacy protocols) as it was guaranteed to exist on every switch.
Placing user traffic on this vlan introduces additional variables that could impact the control plane traffic.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I wouldn't worry about it. In Meraki land, spanning tree protocols only use the untagged VLAN. They need that to flow to let spanning tree form properly.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
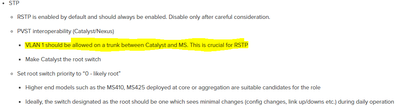
Guys, Meraki best practice lists that VLAN 1 should be allowed on a trunk between a Catalyst and MS Meraki switch. Please see picture below.
However, Cisco best practice recommends to remove VLAN 1 from trunks. I have it removed and it seemed to work fine. So, what are your recommendations?
Thank you in advance,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I disagree, I prefer to avoid VLAN 1 whenever possible.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Meraki switches use VLAN 1 to send and receive BPDU's for STP.
If you block VLAN 1 on the link between the Catalyst and Meraki switches, they won't see each other in the STP topology.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can simply change the default VLAN.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You meant to create a Management vlan and use it as Native and listed in allowed?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That's what I thought. Thks