- Technical Forums
- :
- Wireless
- :
- VPN tunnels on MX600: Anyway to find out the source AP?
VPN tunnels on MX600: Anyway to find out the source AP?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
VPN tunnels on MX600: Anyway to find out the source AP?
We have an increasing amount of guest and employee WiFi tunnels terminating onto a MX600. Is there anyway to quickly identify the source (AP) of the tunnel?
We use centralised DHCP and for the above we have 2 x /21 subnets servicing guests and staff at approx 450 sites. Is there anyway of quickly identifying where a specific client has originated from?
Many Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
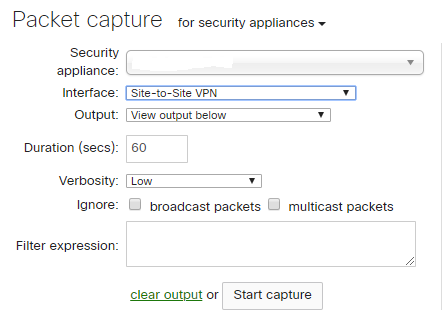
I'm not fully understanding what you are trying to identify. But I typically do a packet capture of the tunnel traffic to try to identify these types of things. But perhaps you are referencing Client VPN? Anyways, I dump the output to Wireshark and sort by utilization.
If this was helpful click the Kudo button below
If my reply solved your issue, please mark it as a solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks man...
Client 'A' is connected to SSID 'Guest' on Access Point 'A' ...tunneled to MX600 on VLAN 110
Then mr administrator comes along and wants to identify where client 'A' is connecting from as administrator see's client 'A' is streaming nothing but YouTube clips of Cristiano Ronaldo, so instead of simply blocking them, they want to be able to identify which AP the tunnel originates.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Without visibility into Access Point A that could be hard to identify. By its nature, a tunnel will hide a lot of that information. On the MX600 side of things, they'll just see client A as a locally connected client with a lot of traffic. To dive deeper into that client's local connection you'd for sure have to look into the network with Access Point 'A'.
But what is he ultimately trying to accomplish? Can't he just use a policy to limit the traffic so he doesn't have to constantly investigate that kind of stuff?
If this was helpful click the Kudo button below
If my reply solved your issue, please mark it as a solution.