- Technical Forums
- :
- Wireless
- :
- Syslog messages don't appear in file
Syslog messages don't appear in file
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Syslog messages don't appear in file
Hello,
We have 4 access point to deliver Wifi Public. We have to keep 1 year of logs.
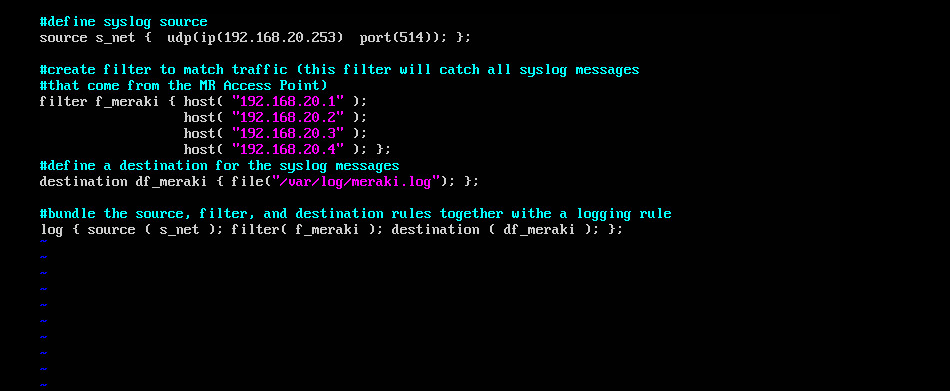
I configured a syslog server on Ubuntu. I followed the technical documentation on Cisco Meraki :
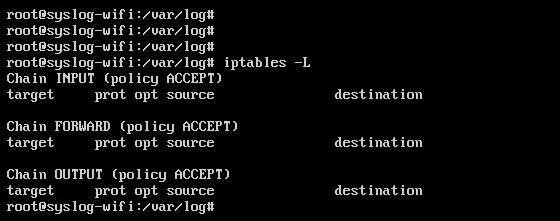
My 514 port is open on my server.
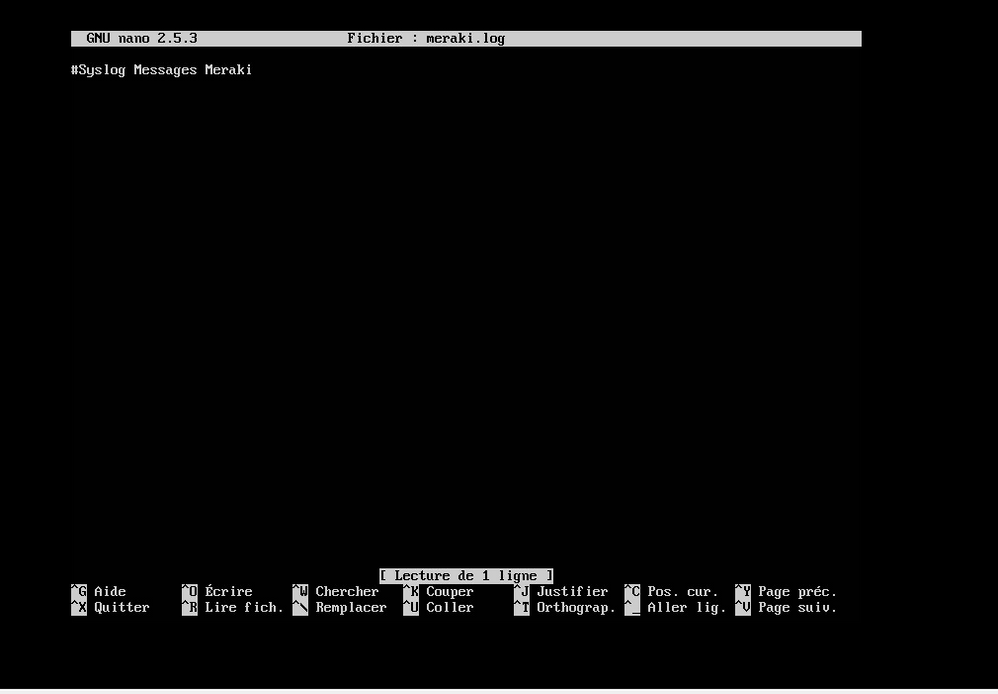
But still don't have the log on my file that i have defined in syslog-ng.conf
If someone has an idea et can help me
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I can't see anything out of the ordinary from your configuration, this all appears to look fine. I assume you've applied the syslog server settings to the correct network which the AP's are in? I assume they're Management IP's are the ones you've got listed in the .Conf file?
Have you tried taking a packet capture from the switch interface that the Syslog server is connected to? This will allow you to see if syslog messages are even hitting the server.
Found this helpful? Give me some Kudos! (click on the little up-arrow below)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi WANKiller,
Thanks for your feedback.
Effectively, the syslog server is on the same network wich the AP are.
To separate the wifi public from our lan, i created a vlan without IP address for the wifipublic on our catalyst 4500.
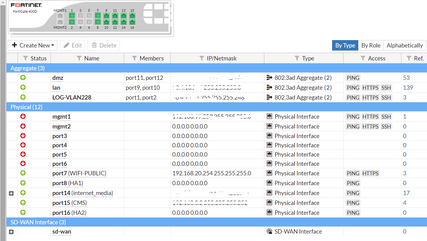
We dedicate an ethernet port on our firewall (fortinet) (attachement1) and give to this physical interface an IP (IP who is the gateway of our meraki AP) like a wire mode
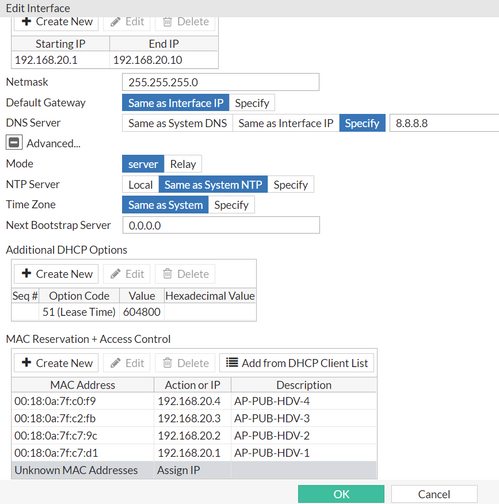
I edited --> DHCP, DNS for the AP (attachement 2)
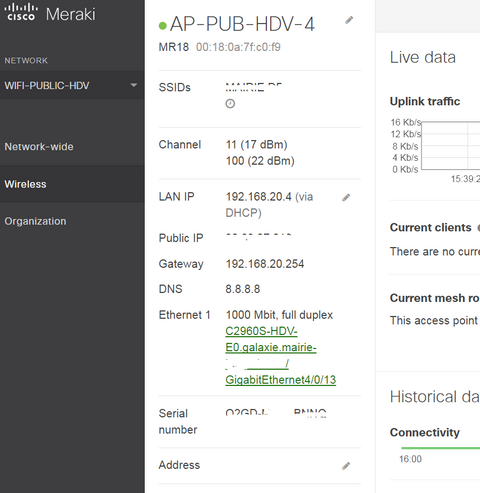
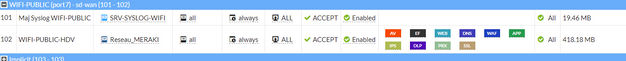
On my meraki dashboard i can see that my AP recover well An IP (ex : attachement3) and my ipV4 policy is ok (attachement 4)
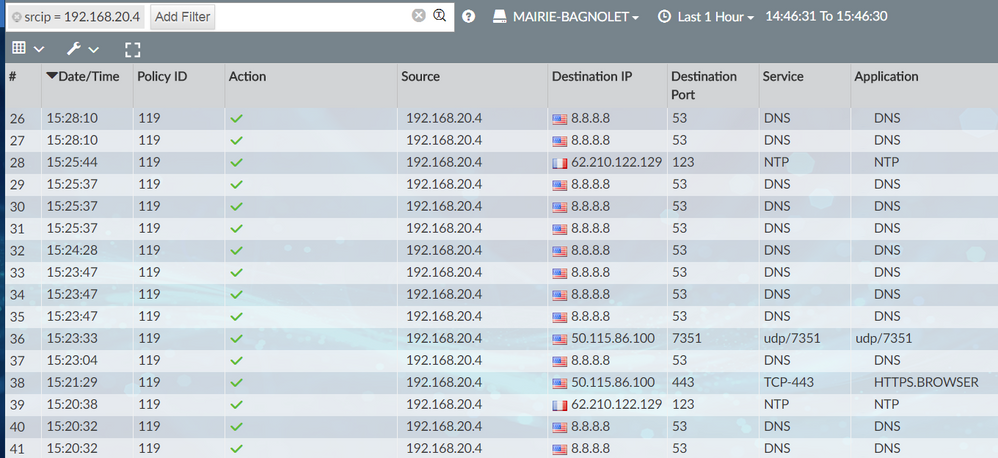
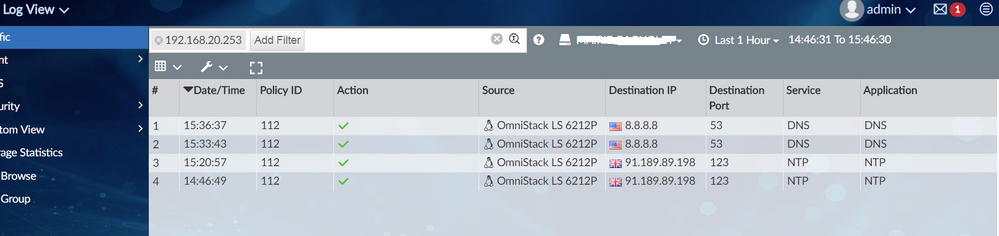
I checked on our analyzer the traffic, we see traffic (DNS,NTP) from the syslog, AP but not for the logs on port 514 (attachement5,6)
Thanks for your help
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Have you configured the dashboard? Refer to the section "Configure Dashboard" in this document:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ok, so looking at your Configuration you have a VLAN terminating (Default gateway) which is on the fortinet. 192.168.20.254/24. The AP's and Syslog are all in this VLAN -
AP's
192.168.20.1/24
192.168.20.2/24
192.168.20.3/24
192.168.20.4/24
Syslog
192.168.20.253/24
If this is the case, what mode are you using for the Guest SSID? I assume with this arrangement you'll be using Mearki NAT mode? As this would be the only way you provide true segregation for Guest traffic as per your proposed design?
What is the firewall rule policy on your Fortinet and what does that refer too? (Attachment 4) you've uploaded?
Found this helpful? Give me some Kudos! (click on the little up-arrow below)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello WANKiller,
Back after the week-end. Thanks for your return.
Yes i'm using Meraki Nat mode. By this way, we separate the public wifi network from our lan.
On the fortinet, the policy rule consists of allow the traffic from WIfi-Public interface (source network Meraki) to all destination and all services. We apply some security profiles :
- Antivirus
- Webfilter
- DNS Filter
- Application control
- IPS
- ANTI-SPAM
- DLP Sensor
- Web Application Firewal
- Proxy Options
- SSL/SSH inspection
What is strange is that if the firewall prevented flows to the syslog on port 514, I should see them.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello PhilipDath,
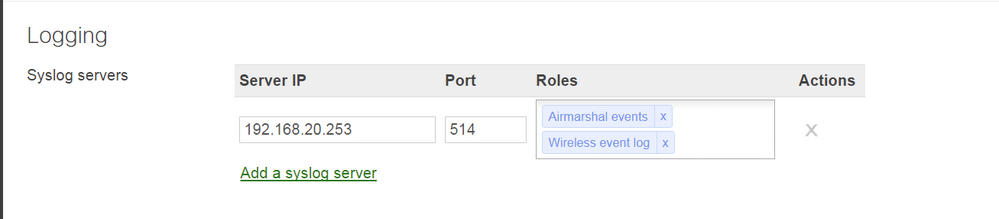
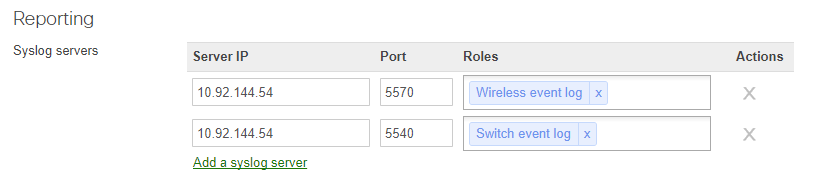
Yes i have configured the dashboard with the syslog ip server on port 514
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The access points and the syslog server are in the same subnet - so you wont see that traffic going through the firewall.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
On the web page Syslog Server Overview and Configuration, in the exemple the devices are on the same subnet