- Technical Forums
- :
- Wireless
- :
- MR Firewall Rules for One SSID
MR Firewall Rules for One SSID
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MR Firewall Rules for One SSID
Wondering if anyone could help out with a scenario we are running into. In the past we have been using a Guest network with a PSK and then registering Guests and manually setting expiration times. This worked fine until now as there are only a couple of us managing a much larger scale solution now and the other group that was helping us no longer wants to play.
we have the blessing from our Information Security team to use a SSID with a PSK and a Click through splash page with some legal jargon. Beyond that, they want us to lock down the SSID as much as possible to the point that only ports 80 and 433 would be open as our guests shouldn't need to be doing much beyond that on this SSID. If other uses cases do come up then we can alter it, but for the time being this is what we are running with.
I imagined that the rules would have looked something like this, but its not working as intended. Support said probably because the Deny Any/Any rule isn't allowing DNS. Anyone have any recommnedations?
# Policy Protocol Destination Port Comment
1 Allow TCP Any 80
2 Allow TCP Any 443
3 Deny Any Any Any
4 Any Local LAN Any Any Wireless clients accessing LAN
5 Allow Any Any Any Default rule
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
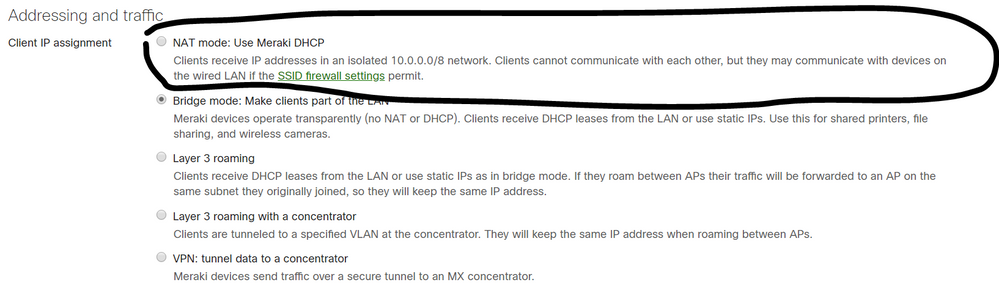
Why not just use Meraki DHCP. It doesn't talk to the LAN side unless you allow.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We have discussed that as well, but maybe I did not express the concern very well.
Their concern is around a Visitor using our Wi-Fi to do something malicious while onsite not only to our internal assets, but they want to try and regulate our Wi-Fi being used to do something externally. Obviously things can and will happen but they would like visitors to only have access to Ports 80 and 443 and nothing else.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
does it work when you add bootp and dns Ports to your dhcp and dns servers
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Nembrey3 I apologize. You can also control what is accessed through "Firewall and traffic shaping" to control bandwidth and even do Layer 7 rules. i.e deny Social media, Proxy, etc.