- Technical Forums
- :
- Wireless
- :
- Certificate based Authentication and Autoconnect to AP's
Certificate based Authentication and Autoconnect to AP's
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Certificate based Authentication and Autoconnect to AP's
I am trying to convert our system and locations from using our External SSO Radius servers for User/Pass authentication to Certificate based auth so users will have zero interaction while connecting but I need to make it as secure as possible. Has anyone successfully done this using the Meraki APs?
I have the CA and NPS server running and connected to the SSID but to get the clients to connect I have to select
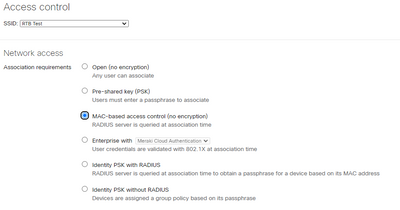
MAC-based access control (no encryption) which means there is no encryption.
How do I keep the connection encrypted and use a certificate that we shoot out via GPO along with the NPS connection profile?
- Labels:
-
Installation
-
Other
-
SSID
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You need to use WPA2-Enterprise mode. It's quite a bit of work. I would start by getting it going using username/password.
Then you need to move on to creating a group policy and have it deploy machine and user certificates to all AD computers, and once that is done update the NPS policy to require certificate-based authentication.
This will be a steap learning curve if you haven't done this before.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Maybe I wasn't clear enough but we have user/pass already working with our External SSO IDPs. I already have NPS and the CA configured and done and it works in a test network on the SSID I'm using. The problem is the selection of encryption methods with a Certificate based authentication is set to "OPEN" which I do not want.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You need to create a group policy to configure the WiFi settings on the machines. You can use either EAP-TLS, or PEAP+EAP-TLS.
Then in NPS you need to configure it to accept the same authentication method.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Correct which I have. My issue is related to Meraki though and the configuration of the SSID access. So to get it to work I had to pick the radio button currently selected:
This will not encrypt any connections which is the problem here.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
And that is where you select "Enterprise with (dropdown) My Radius server" - Setup your NPS in the radius server fields , setup your rules in NPS to use EAP-TLS , and have your CA issue certificates to your devices (typically done via a GPO and CertTemplate).
We do this a lot of places, with both Meraki and Cisco Classic. Using NPS or Cisco ISE as "your" radius server. It is the most secure you cant get if you remember to setup the client correctly also 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you I will test with those settings in Meraki. Just in the first few tests I do notice that the logs containing the Success and deny logs show the Computer/user as anonymous. Seeing is how the Policy is looking for a Machine cert that makes somewhat sense but I don't suppose there is a way to audit the user as well in the logs?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You need to use something like TEAP with EAP chaining which modern Windows 10 does support, but Microsoft NPS does not. EAP chaining allows you to authenticate both the user and computer together.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ok we can use other ways of user auditing instead then but now how would I get mobile devices (iPhone and iPads) to adopt the cert authentication through the meraki SSIDs. They still seem to prompt for a User/Pass after I have setup the NPS server, set the Radius in Meraki and the CA is working as this solution works just fine on test laptops.
This solution works for out Windows devices but I have read Meraki's solution for the mobile devices and cert auth is as such here:
That will change the Radius server to Meraki Authentication so then that screws up the solution for the laptops.