- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Retrieving the LDAP list from AD is intermittent at best.
Retrieving the LDAP list from AD is intermittent at best.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Retrieving the LDAP list from AD is intermittent at best.
Hi all,
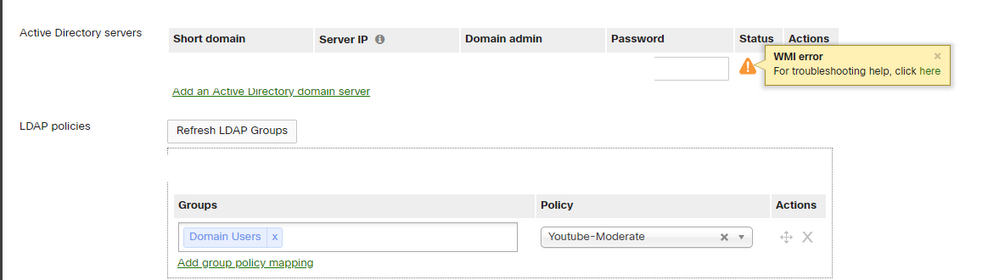
We are trying to enable the AD connector on a number of MX appliances spread across our European offices but failing in what seems to be a completely random fashion. We've followed the setup process outlined in the following article on each of the DC's we are trying to work with and confirm all of the relevant settings are in place.
When we add the AD credentials (We're using the same service account with just the relevant permissions), we can get the status to report back as OK but getting the LDAP group list to populate is where we are falling over. It seems to be completely random whether it works or not. We appreciate that we need to point to the sites local DC to capture the login details but even that's not consistent.
For example, our office in The Netherlands has been failing talking to its local DC but worked (for the first time today) when pointed at one in the UK. On the same UK site, their local MX refuses to talk to the same DC that is happily working for MX in The Netherlands. This seemingly random pattern repeats itself across half a dozen different sites and I cannot find any one link between them.
Does anyone have a clue what could be causing this?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Anything interesting reported in the Windows event log at the times the MX tried to talk to it?
Any third party sofwtare firewall or antivirus software on the Windows AD controllers? If so, perhaps try temporarily disabling that software to see if it is related.
Do the AD servers have certificates installed to allow LDAPS?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'll ask our server team to double check but there was nothing that jumped out last time. We do have the Symantec AV client installed on all of the DC's, all running the same policy but some happily respond and others don't, but not consistently. MX1 might get a response from DC1 but MX2 doesn't.
I'm not 100% certain how to confirm the certificates but is one MX works and another doesn't, I would have thought the certificate was OK.
I'm just finding it difficult to find a pattern to be able to poke something with a stick.