- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Block access to the guest network when the LTE circuit is active
Block access to the guest network when the LTE circuit is active
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Block access to the guest network when the LTE circuit is active
Please, I have been trying to figure out how to block access to the guest network on guest WIFI SSID when the LTE circuit is active which is WAN1. The primary link is DSL which is WAN2 and needs assistance to sort this out
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
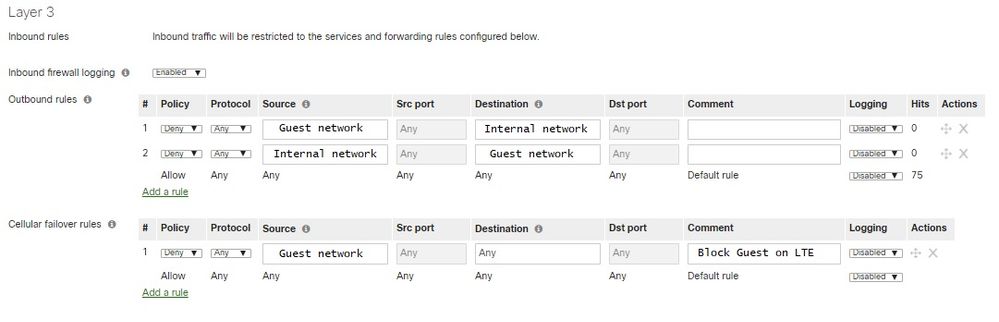
On the firewall page there's a section for LTE specific rules that only apply when the MX is on cell. You can block your guest networks from using the LTE there.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi jdsilva, that only applies if It's connected via USB. My MX is connected via WAN interface
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ooooh! Sorry, I think I misunderstood.
You have LTE connected to WAN1? So you have an LTE router of some kind? Not a USB modem?
If you're using an LTE router/modem connected via Ethernet to WAN1 then you can't do what you want. Sorry 😞
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ok, I will call Meraki support if they have any workaround to get it resolved. Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This might be more than you would like to do, but you could try something with VLANs and DNS.
If you have your guest SSID on a separate VLAN then under the Security appliance DHCP settings you can change the DNS nameserver to "Proxy to upstream DNS", and them remove DNS settings from the Cellular modem. That would effectively make that VLAN useless to most users when using the cellular modem. (You might have someone that can figure out to set their own DNS, but would at least limit the number of users)
You would still allow other VLANs to work by setting a DNS server under the DHCP settings on the Security appliance.
This is just a thought, so you would definitely want to test it out before going to production with it and relying on it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This can be done, and I do this myself as my backup LTE is a hotspot box that has a LAN port that plugs into my firewall, so it is not USB based.
This is actually easier than you think, however you will need to contact support.
One of the gripes I've always had about the firewall section on the MX is they do not separate WAN1 and WAN2 firewall rules. They combine WAN1 and WAN2 into a single 'Outbound rules' section. They should separate them into two groups so that you have granularity control over it. Rumor is that they are planning on doing this in the future, but we'll see.
However, if you ask support, they can do something behind the scenes, so that the 'cellular' firewall rules are actually applied to WAN2
So when WAN1 goes down, the cellular failover rules 'append' themselves up, to the outbound rules above. So just think of the 'cellular failover rules' section as 'WAN 2 outbound rules'.
Here is an example of my setup (i took out any IP info to make it easier)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Forgot to mention that you will need your primary uplink to be WAN1 for my solution. I see original poster has WAN2 as primary, so just clarifying.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
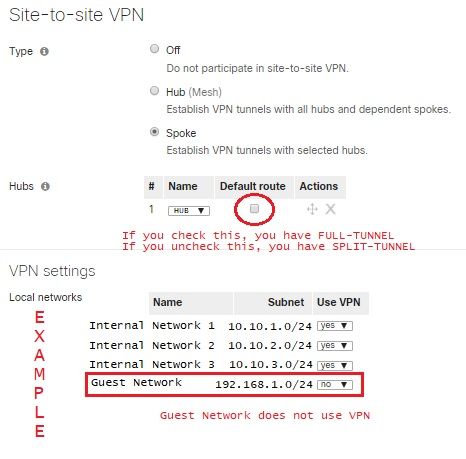
I have tried the above option and others with Meraki support team but still not working. I can still connect to the internet vis my LTE WAN interface . I have my network setup for SDWAN as Hub and Spoke topology
I was told by support rep that If your network is designed as Hub and Spoke, this cellular failover can never work because it's going through the VPN tunnel. Support team has sent this case to their deployment team for further input and I will update this conversation for the outcome.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Spence,
For my solution you will need to have your primary ISP as WAN1 (your DSL) and your secondary (LTE) as WAN2. Then my setup should function as long as you have support make the 'cell firewall rules' apply to WAN2.
However if your doing Full-tunneling then all your traffic will go over the AutoVPN to your HUB, so any 'local' internet usage will go over that and you can't block it (that I'm aware of).
You would need to do split tunnel and then only send intra-net (internal) traffic over your AutoVPN tunnel. This way Internet traffic will drop off locally, either WAN1 and WAN2, and then with my method you can block guest to Internet over WAN2 (LTE) when it kicks in.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@MacuserJim good thinking, but without DNS the MX will have trouble talking to the Meraki Cloud itself when on the 4G connection.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
-
3rd Party VPN
167 -
ACLs
102 -
Auto VPN
314 -
AWS
39 -
Azure
72 -
Client VPN
441 -
Firewall
629 -
Other
595