- Technical Forums
- :
- Mobile Device Management
- :
- Re: Sync AD Groups Over
Sync AD Groups Over
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sync AD Groups Over
Hi Folks,
I finally got a Windows Server 2012 R2 lab setup with AD. I have verified that I can enroll devices with a user from AD, but I can't seem to sync over any AD groups in Meraki. I feel it is the way I am setting my AD groups up in Windows Server. Could anyone provide a sample group they configured that syncs to Meraki?
Thanks!
Jared
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Just a warning: This is my first time ever touching Windows Server and Active Directory. I configured this all from Youtube videos.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
AD can be configured in many places for different things. Where are you doing it?
I'm going to guess that it may need ldaps, and you'll need to use a certificate on your AD controller (can be free private), or perhaps the permissions are not allowing it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The Server is running in a virtual machine.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@PhilipDAth I enabled a certificate on the server using LDAPS and switched the port on my Meraki configuration to use 636. My AD sync is still failing, the funny part is that when I go to m.meraki.com and log in with my AD credentials it works and that specific user syncs over but the groups they are a member of do not sync over. Any other tips you recommend?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In the Meraki dashboard; where are you configuring AD? It can be done in several places. Once I know I can give you some screen shots.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
For some reason I can’t upload a screenshot from my phone. But, it is under Systems Manager > Configure > General Heading > User Authentication Settings
Thanks,
Jared
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Under:
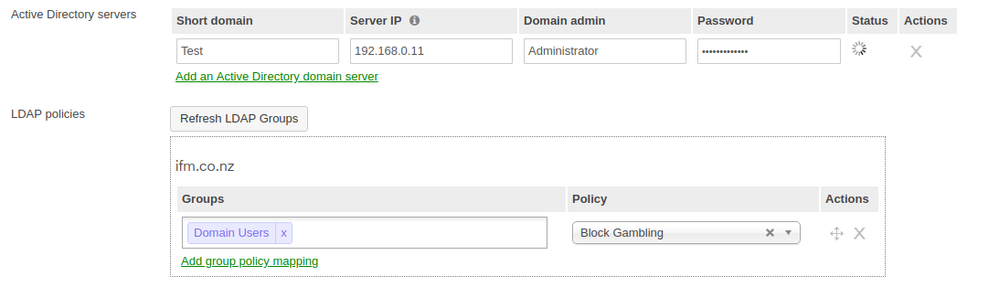
Security Appliance/Active Directory does it look something like this:
You have definitely promoted the server to be an AD Controller?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Funny part is that I don’t see the LDAP policies section. I have promoted the server to a domain controller. I am going to give support a ring.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Does the "Status" have a green dot it in, showing it can talk to AD okay?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
what was your solution ???
I found this guide
https://documentation.meraki.com/MX/Content_Filtering_and_Threat_Protection/Active_Directory_Integra...
I have to map
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@nst1 we did these settings on our AD aswell, but you don't need to do this. This docs are referencing if you are integrating your AD through a MX Firewall. We use an enrolled device as Gateway.
Did the same thing already with a Windows VM which is used as AD (enrolling in SM and using it as Gateway for AD access). No need to configure these things as mentioned in the docs you linked.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
in my case, add the AD to the MX with the user and password and everything looks fine, update the groups and I can see them.
Only that a new group was created in the AD and when updating the groups this new group did not loveo.
I do not administer the AD and therefore I asked the person who administers the AD to check if the group is mapped.